KubeVirt v1.8 introduces a Hypervisor Abstraction Layer enabling support for multiple virtualization backends beyond KVM, along with confidential computing capabilities and performance improvements for AI workloads.
The CNCF's KubeVirt project has released version 1.8, marking a significant evolution in cloud-native virtualization. The release, announced at KubeCon + CloudNativeCon Europe 2026, introduces a Hypervisor Abstraction Layer (HAL) that breaks KubeVirt's long-standing dependency on KVM, while adding confidential computing support and performance optimizations for AI and HPC workloads.

Breaking Free from KVM
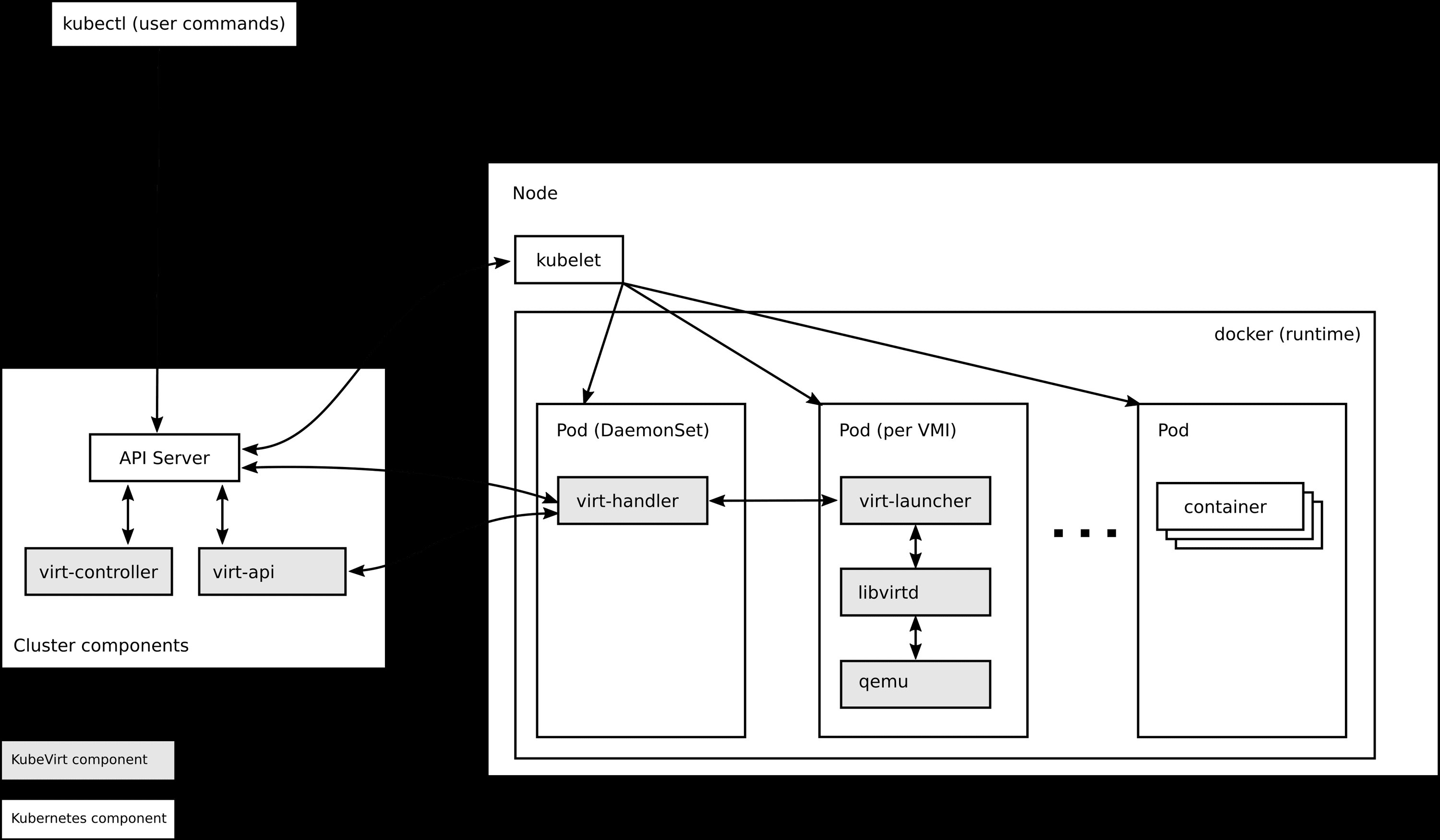
For years, KubeVirt has been tightly coupled to KVM as its underlying hypervisor technology. This architecture served well for organizations running Linux-based workloads but limited adoption in environments requiring different virtualization backends. The new Hypervisor Abstraction Layer fundamentally changes this equation.
The HAL allows KubeVirt to integrate alternative virtualization management modules (VMMs) while maintaining backward compatibility with existing KVM-first deployments. This architectural shift was previewed by Vladik Romanovsky of Red Hat at KubeCon NA 2025, where he noted the project was "exploring support for multiple VMMs beyond QEMU/KVM." The v1.8 release transforms that exploration into production-ready infrastructure.
This abstraction layer enables organizations to choose the most appropriate hypervisor for their specific workloads. Enterprises with mixed environments—perhaps running some workloads on KVM while others require different virtualization technologies—can now consolidate their infrastructure under a single Kubernetes control plane rather than maintaining parallel management systems.
Confidential Computing for Sensitive Workloads
Security-conscious organizations will find the confidential computing enhancements particularly compelling. The release adds Intel TDX (Total Memory Encryption) attestation support, allowing virtual machines to cryptographically verify they're running on confidential hardware before processing sensitive data.
This capability addresses a critical gap in cloud-native virtualization. Organizations handling regulated data, intellectual property, or other sensitive information can now run these workloads on KubeVirt with cryptographic guarantees about their execution environment. The attestation mechanism ensures that VMs can prove they're running in a trusted execution environment, preventing tampering or unauthorized access to memory contents.
Performance Optimizations for AI and HPC
The v1.8 release includes several performance-focused enhancements aimed at demanding workloads. PCIe NUMA topology awareness allows better placement of virtual machines relative to hardware resources, reducing latency for memory-intensive operations. Combined with other resource improvements, the community claims these changes enable "near-native performance" for AI and high-performance computing workloads.
These optimizations are particularly relevant as organizations increasingly run machine learning inference and training workloads alongside traditional applications on Kubernetes clusters. The ability to achieve near-native performance while maintaining the operational benefits of container orchestration represents a significant value proposition for enterprises with mixed workload requirements.
Networking and Storage Enhancements
On the networking front, the user-space network connectivity binding plugin "passt" has graduated from plugin status to become a core component. This promotion reflects its maturity and importance to the project's networking architecture. Additionally, engineers can now live-update Network Attachment Definition (NAD) references without restarting virtual machines, enabling dynamic network reconfiguration for running workloads.
The project has also decoupled KubeVirt from NAD definitions at the virt-controller level. This architectural change reduces API calls and eliminates permissions previously required for VM activation at scale, improving both performance and security posture.
Storage engineering introduces two notable features. The ContainerPath volume type allows direct mapping of container paths for VM storage, described by maintainers as an "escape hatch" for cloud provider credential injection patterns. This feature addresses a common operational challenge in hybrid cloud environments where VMs need access to cloud-specific credentials or configuration data.
The second storage enhancement is Incremental Backup with Changed Block Tracking (CBT). Leveraging QEMU and libvirt backup capabilities, this feature enables storage-agnostic incremental VM backups. The maintainers claim this approach delivers faster backups and significantly reduces storage footprint compared to full backups, addressing a common pain point in VM management.
Scaling to Production Workloads
Scale and performance work in v1.8 includes expanding the test framework to 8,000 virtual machines. The maintainers report a linear increase in memory usage for the virt-api and virt-controller components, presenting these figures as scaling estimates they intend to publish with each release. This transparency helps organizations understand resource requirements for production deployments.
Pure Storage's Portworx unit has been pushing KubeVirt's boundaries in production. They announced Portworx for KubeVirt at Red Hat Summit 2025, positioning it as a practical alternative hypervisor with claimed cost reductions of up to 50%. The company later reported running more than 5,000 virtual machines on KubeVirt in production environments, driven by cost mandates that made traditional virtualization economically unfeasible.
Benchmarking and Vendor Neutrality
A talk scheduled at KubeCon EU 2026 by Bhumitra Nagar and Dhruv Bhatnagar of Pure Storage addresses a critical gap in the ecosystem. Titled "KubeVirt Benchmarking at Scale: A Vendor-Neutral End-to-End Testing Framework for Cloud Native Virtualisation," the presentation introduces a framework for testing KubeVirt at scale across vendors.
This work complements the community's own KWOK benchmarks while approaching the problem from a storage and vendor neutrality angle. As KubeVirt gains adoption, having standardized, vendor-neutral benchmarks becomes increasingly important for organizations evaluating the technology against traditional virtualization platforms.
The Road to Graduation
Since moving to CNCF incubation status in 2022, KubeVirt has added significant capabilities including GPU assignment, NUMA support, live migration, and common instance types. Organizations including Arm, CoreWeave, and Kubermatic were already using production-level solutions at that time.
CloudNativeNow noted in mid-2025 that KubeVirt is "designed for teams focused on DevOps that have or want to adopt Kubernetes and also have virtual machine workloads that cannot be easily containerised." The Hypervisor Abstraction Layer positions the project to extend beyond Linux KVM dependency, while confidential computing and AI performance work address enterprise requirements that have historically steered organizations toward proprietary virtualization platforms.
Vladik Romanovsky mentioned at KubeCon NA 2025 that reaching CNCF graduation is a milestone the project is working toward. Whether KubeVirt achieves this status depends on how the graduation process continues to mature and how the community addresses the requirements for production readiness at scale.
"It's wonderful to see new contributors coming forward with exciting ideas and engage with the project to see them through," the KubeVirt Community writes in the release announcement. The post also notes that "the next release is looking to be larger still," suggesting the project's momentum continues to build.
The v1.8 release represents four years of work under CNCF's aegis and positions KubeVirt as a serious contender in the virtualization landscape. By addressing the limitations of container-only approaches while maintaining Kubernetes' operational benefits, KubeVirt offers a pragmatic path for organizations modernizing their infrastructure without abandoning existing VM investments.
For teams struggling with the container versus VM dichotomy, KubeVirt v1.8 provides a compelling alternative: unified management, improved security through confidential computing, better performance for demanding workloads, and the flexibility to choose the right virtualization technology for each use case.

Comments
Please log in or register to join the discussion