Microsoft Defender for Containers now includes runtime malware detection and binary drift prevention, providing last-line defense against container-based attacks through integrated sensor technology and cloud protection.
Runtime malware protection has become essential for cloud-native environments as traditional image scanning alone cannot stop attacks that occur during container execution. Microsoft Defender for Containers now provides comprehensive runtime workload security that monitors container activity, detects malware, and prevents binary drift throughout the container lifecycle.
The Evolution of Container Security
Many organizations focus primarily on scanning container images before deployment, but this approach leaves critical gaps. While image scanning protects against known vulnerabilities in the build phase, it cannot prevent malware that enters through compromised CI/CD pipelines, exposed services, or misuse of administrative tools. Runtime malware detection serves as the essential last line of defense when preventive controls fail.
Malware that executes successfully inside a container can attempt privilege escalation, container escape, and ultimately compromise the host system. This makes runtime protection not just an enhancement but a fundamental security requirement for production environments.
How Defender for Containers Antimalware Works
The antimalware feature in Defender for Containers is powered by Microsoft Defender Antivirus cloud protection and provides near-real-time malware detection directly within container environments. The solution is available via Helm with sensor version 0.10.2 for Azure Kubernetes Service (AKS), Google Kubernetes Engine (GKE), and Amazon Elastic Kubernetes Service (EKS).
Three Core Components
The protection system consists of three main components that work together to provide comprehensive security:
1. Defender Sensor The sensor runs inside Kubernetes clusters and monitors workload activity in real time. It provides runtime visibility into container processes, binary execution monitoring, behavioral inspection, and the ability to alert and block malware execution. The sensor supports multicloud environments and uses outbound-only connectivity, requiring no inbound access.
2. Antimalware Policy Engine Policies define the response when malware is detected, offering options for alert-only, blocking execution, or ignoring specific cases. Organizations can scope policies to Azure subscriptions, AWS accounts, GCP projects, or specific clusters, namespaces, pods, images, labels, or workloads. This granular control helps reduce false positives while maintaining strict security where needed.
3. Cloud Protection The system integrates with Microsoft Defender Antivirus cloud protection, which provides global threat intelligence, machine learning classification, reputation scoring, and zero-day detection. When suspicious binaries appear, cloud analysis determines whether they should be allowed or blocked.
Host vs. Workload Protection
Antimalware rules can be applied to different resource scopes, protecting both container workloads and host nodes. Workload protection covers processes inside containers, while host protection secures the Kubernetes node OS and runtime. This dual-layer approach is critical because attackers often attempt to escape containers and target kubelet, container runtime, and node filesystem. Blocking malware at both layers prevents cluster takeover.
Binary Drift Detection and Prevention
Beyond malware detection, Defender for Containers addresses binary drift - a critical security concern in containerized environments. Containers are expected to be immutable, with running containers executing only binaries from the original container image. Most container attacks involve downloading malware, installing crypto miners post-compromise, or installing attack tools dynamically.
The sensor detects runtime drift such as new binaries downloaded after deployment, files written to the container filesystem, tools installed via reverse shell, or payloads dropped by attackers. When drift is detected, the sensor prevents it from occurring and generates alerts.
Testing and Validation
Organizations can test the malware detection capabilities by uploading an EICAR test file to a running container. When policy action is set to block malware, the sensor kills the malicious process and generates alerts in both Defender for Cloud and Defender XDR portals. Security operations teams can investigate incidents and take response actions through the Defender portal.
Implementation Requirements
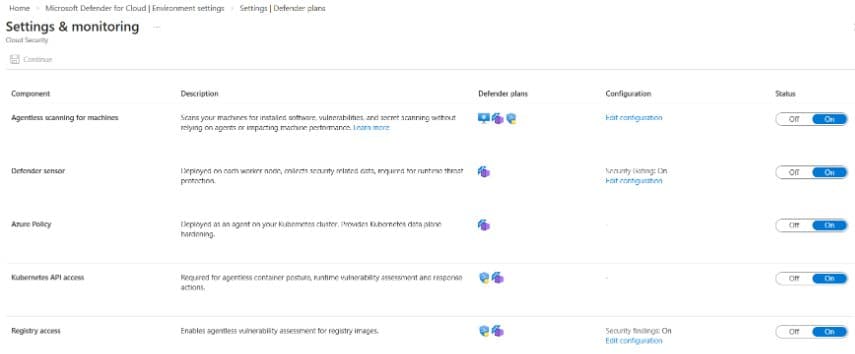
To implement Defender for Containers antimalware, organizations need to ensure sufficient Kubernetes cluster resources and outbound connectivity. The sensor requires specific CPU and memory allocations beyond core requirements, and all components use outbound-only connectivity. Prerequisites include enabling the Defender sensor, security findings, registry access, and Kubernetes API access.
The solution represents a significant advancement in container security, moving beyond traditional image scanning to provide active runtime protection that can detect and prevent attacks as they occur. This comprehensive approach addresses the full spectrum of container security threats, from initial compromise to lateral movement and persistence attempts.
For organizations running containerized workloads in production, runtime malware detection and binary drift prevention are no longer optional enhancements but essential security controls that protect against the evolving threat landscape in cloud-native environments.
Comments
Please log in or register to join the discussion