Microsoft has uncovered a sophisticated ClickFix social engineering campaign that exploits Windows Terminal to deploy Lumma Stealer malware, bypassing traditional security detections and targeting browser credentials.
Microsoft on Thursday disclosed details of a new widespread ClickFix social engineering campaign that has leveraged the Windows Terminal app as a way to activate a sophisticated attack chain and deploy the Lumma Stealer malware. The activity, observed in February 2026, makes use of the terminal emulator program instead of instructing users to launch the Windows Run dialog and paste a command into it.
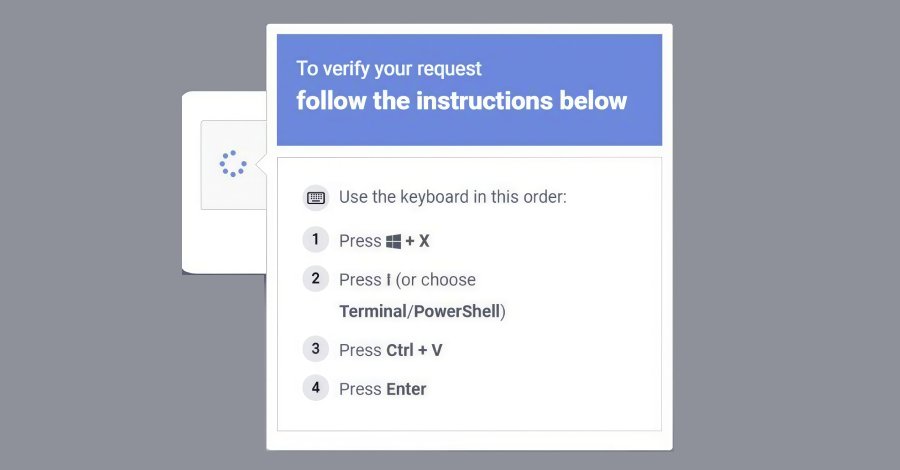
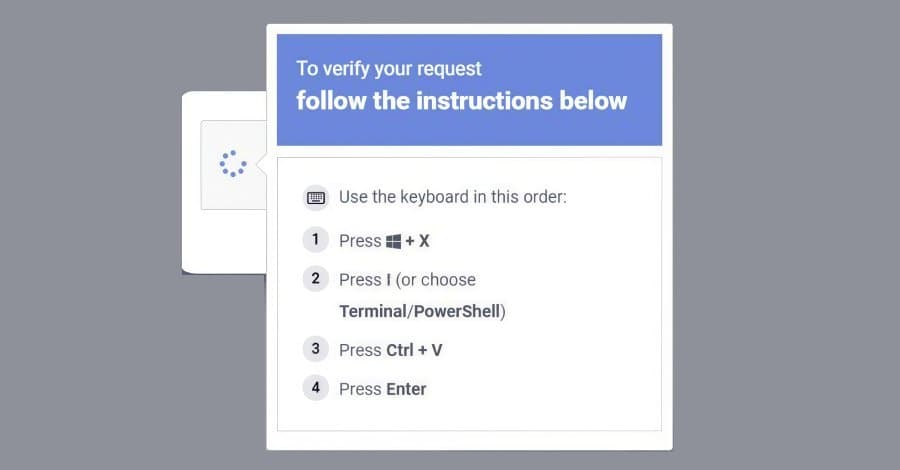
"This campaign instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly, guiding users into a privileged command execution environment that blends into legitimate administrative workflows and appears more trustworthy to users," the Microsoft Threat Intelligence team said in a series of posts on X.
What makes the latest variant notable is that it bypasses detections specifically designed to flag Run dialog abuse, not to mention take advantage of the legitimacy of Windows Terminal to trick unsuspecting users into running malicious commands delivered via bogus CAPTCHA pages, troubleshooting prompts, or other verification-style lures.
The post-compromise attack chain is also unique: when the user pastes a hex-encoded, XOR-compressed command copied from the ClickFix lure page into a Windows Terminal session, it spans additional Terminal/PowerShell instances to ultimately invoke a PowerShell process responsible for decoding the script. This, in turn, leads to the download of a ZIP payload and a legitimate but renamed 7-Zip binary, the latter of which is saved to disk with a randomized file name. The utility then proceeds to extract the contents of the ZIP file, triggering a multi-stage attack chain that involves the following steps:
- Retrieving more payloads
- Setting up persistence via scheduled tasks
- Configuring Microsoft Defender exclusions
- Exfiltrating machine and network data
- Deploying Lumma Stealer using a technique called QueueUserAPC() by injecting the malware into "chrome.exe" and "msedge.exe" processes
"The stealer targets high-value browser artifacts, including Web Data and Login Data, harvesting stored credentials and exfiltrating them to attacker-controlled infrastructure," Microsoft said.
The Windows maker said it also detected a second attack pathway, as part of which, when the compressed command is pasted into Windows Terminal, it downloads a randomly named batch script to the "AppData\Local" folder by means of "cmd.exe" in order to write a Visual Basic Script to the Temp folder (aka %TEMP%).
"The batch script is then executed via cmd.exe with the /launched command-line argument. The same batch script is then executed through MSBuild.exe, resulting in LOLBin abuse," it added. "The script connects to Crypto Blockchain RPC endpoints, indicating an etherhiding technique. It also performs QueueUserAPC()-based code injection into chrome.exe and msedge.exe processes to harvest Web Data and Login Data."
What Makes This Campaign Different
Traditional ClickFix campaigns relied on the Windows Run dialog (Win+R) to execute malicious commands, which security tools have become adept at detecting. By shifting to Windows Terminal, attackers have found a way to blend their malicious activities with legitimate administrative workflows.
Windows Terminal is a legitimate Microsoft tool used by system administrators and power users for command-line operations. Its appearance in the attack chain makes the malicious activity appear more trustworthy to end users who might be suspicious of the traditional Run dialog.
The use of hex-encoded, XOR-compressed commands adds another layer of obfuscation, making it harder for security tools to detect the malicious payload through signature-based detection methods.
The Lumma Stealer Threat
Lumma Stealer, also known as LummaC2, is a sophisticated information-stealing malware that has been actively developed and sold on underground forums since at least 2022. It specializes in extracting sensitive data from web browsers, including:
- Stored passwords and login credentials
- Credit card information
- Cryptocurrency wallet data
- Session cookies and authentication tokens
- Browser autofill data
The malware's ability to inject itself into legitimate browser processes like chrome.exe and msedge.exe allows it to harvest data while remaining stealthy, as the malicious activity appears to be coming from trusted applications.
Technical Analysis of the Attack Chain
The attack chain demonstrates several advanced techniques:
Living-off-the-land binaries (LOLBins): The campaign uses legitimate Windows tools like cmd.exe, MSBuild.exe, and 7-Zip for malicious purposes, making detection more difficult.
Process injection: QueueUserAPC() technique allows the malware to execute code within the context of legitimate browser processes.
Persistence mechanisms: Scheduled tasks ensure the malware survives system reboots.
Defense evasion: Microsoft Defender exclusions are configured to prevent detection.
Data exfiltration: The malware targets specific browser databases (Web Data and Login Data) that contain the most valuable information.
Protection and Mitigation
Microsoft recommends several steps to protect against this campaign:
User education: Train users to be suspicious of unexpected CAPTCHA pages, troubleshooting prompts, or verification requests that ask them to run commands.
Application control: Implement policies that restrict the execution of unauthorized scripts and binaries.
Endpoint detection and response (EDR): Deploy EDR solutions that can detect anomalous process behaviors and LOLBin abuse.
Network monitoring: Watch for unusual network connections to cryptocurrency blockchain RPC endpoints and attacker-controlled infrastructure.
Browser security: Configure browsers to limit the storage of sensitive credentials and implement additional authentication mechanisms.
The Broader Context
This campaign represents an evolution in social engineering tactics, where attackers continuously adapt their methods to bypass security controls. The shift from Run dialog abuse to Windows Terminal exploitation shows how threat actors are finding new ways to abuse legitimate tools for malicious purposes.
The use of cryptocurrency-related infrastructure (Crypto Blockchain RPC endpoints) suggests the attackers may be targeting cryptocurrency users specifically, or using blockchain technology to obscure their command and control communications.
As organizations continue to implement stronger security controls, attackers will likely continue to find innovative ways to social engineer users and bypass technical controls. This campaign serves as a reminder that user awareness and behavior remain critical components of a comprehensive security strategy.
Industry Response
The cybersecurity community has responded quickly to this threat, with various security vendors updating their detection capabilities to identify the specific indicators of compromise associated with this campaign.
Security researchers are also analyzing the campaign's infrastructure and techniques to better understand the threat actor's capabilities and potential future developments.
This Microsoft disclosure adds to a growing body of research on ClickFix campaigns, which have been increasingly prevalent in recent months. The technique's effectiveness in bypassing traditional security controls has made it a favorite among various threat actor groups targeting both enterprise and consumer environments.
Comments
Please log in or register to join the discussion