North Korean APT ScarCruft has developed sophisticated new tools including a Zoho WorkDrive backdoor and USB-propagating malware capable of breaching air-gapped networks, marking an evolution in their surveillance capabilities.
The North Korean threat actor known as ScarCruft has developed an alarming new arsenal of surveillance tools, including a backdoor that abuses Zoho WorkDrive for command-and-control communications and USB malware capable of breaching air-gapped networks, according to researchers at Zscaler ThreatLabz.
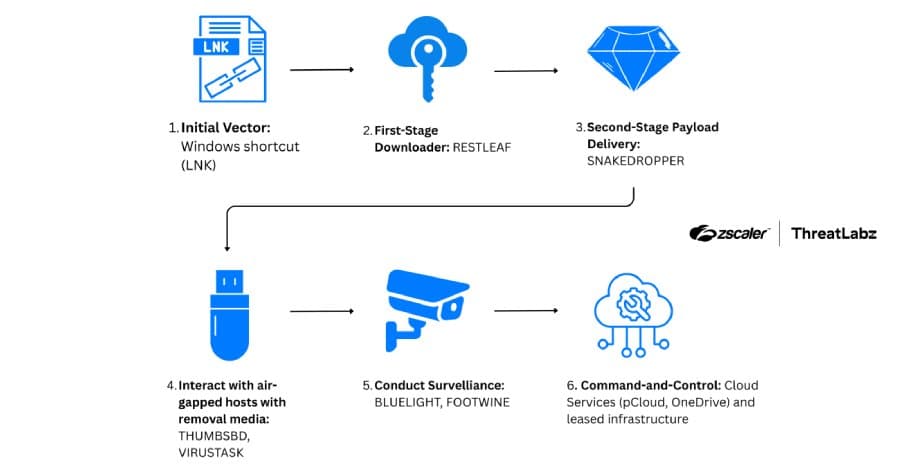
A Multi-Stage Infection Chain
The campaign, dubbed Ruby Jumper, was discovered in December 2025 and employs a sophisticated multi-stage infection process. It begins when victims open a malicious LNK file that launches a PowerShell command to scan the current directory and locate itself based on file size.
"In the Ruby Jumper campaign, when a victim opens a malicious LNK file, it launches a PowerShell command and scans the current directory to locate itself based on file size," explained security researcher Seongsu Park. "Then, the PowerShell script launched by the LNK file carves multiple embedded payloads from fixed offsets within that LNK, including a decoy document, an executable payload, an additional PowerShell script, and a batch file."
The lure documents used in this campaign display articles about the Palestine-Israel conflict, translated from North Korean newspapers into Arabic, designed to appeal to specific target audiences.
RESTLEAF: The Zoho WorkDrive Backdoor
One of the most significant developments in this campaign is RESTLEAF, a Windows executable payload that marks the first time ScarCruft has abused Zoho WorkDrive in its attack campaigns. Once authenticated with Zoho WorkDrive infrastructure using a valid access token, RESTLEAF downloads shellcode that's executed via process injection.
This eventually leads to the deployment of SNAKEDROPPER, which installs the Ruby runtime, sets up persistence using a scheduled task, and drops additional payloads including THUMBSBD and VIRUSTASK.
THUMBSBD: The Air-Gapped Network Penetrator
THUMBSBD represents a particularly concerning development in cyber-espionage capabilities. Disguised as a Ruby file, this malware uses removable media to relay commands and transfer data between internet-connected and air-gapped systems.
"Unlike THUMBSBD which handles command execution and exfiltration, VIRUSTASK focuses exclusively on weaponizing removable media to achieve initial access on air-gapped systems," Park explained.
The malware is capable of harvesting system information, downloading secondary payloads from remote servers, exfiltrating files, and executing arbitrary commands. When removable media is detected, THUMBSBD creates a hidden folder to stage operator-issued commands or store execution output.
FOOTWINE: Comprehensive Surveillance Tool
THUMBSBD delivers FOOTWINE, an encrypted payload with an integrated shellcode launcher that comes equipped with keylogging and audio and video capturing capabilities. This malware communicates with its command-and-control server using a custom binary protocol over TCP and supports an extensive range of commands:
- sm: Interactive command shell
- fm: File and directory manipulation
- gm: Managing plugins and configuration
- rm: Modifying the Windows Registry
- pm: Enumerating running processes
- dm: Taking screenshots and capturing keystrokes
- cm: Performing audio and video surveillance
- s_d: Receiving batch script contents from C2 server, saving it to
%TEMP%\SSMMHH_DDMMYYYY.bat, and executing it - pxm: Setting up a proxy connection and relaying traffic bidirectionally
- DLL loading: Loading specified DLLs
BLUELIGHT and VIRUSTASK: Cloud-Enabled Persistence
THUMBSBD also distributes BLUELIGHT, a backdoor previously attributed to ScarCruft since at least 2021. This malware weaponizes legitimate cloud providers including Google Drive, Microsoft OneDrive, pCloud, and BackBlaze for C2 communications, enabling it to run arbitrary commands, enumerate the file system, download additional payloads, upload files, and remove itself.
VIRUSTASK, delivered as another Ruby file, functions similarly to THUMBSBD but focuses exclusively on weaponizing removable media to achieve initial access on air-gapped systems. This specialization allows for more efficient propagation across isolated networks.
Implications for Air-Gapped Security
The Ruby Jumper campaign demonstrates a significant evolution in how threat actors can compromise air-gapped networks. By combining cloud-based C2 infrastructure with USB-propagating malware, ScarCruft has created a hybrid approach that bypasses traditional network isolation defenses.
Organizations maintaining air-gapped systems should implement strict removable media policies, conduct regular security awareness training, and consider hardware-based controls to prevent unauthorized USB device usage. The use of legitimate cloud services for C2 also highlights the importance of monitoring for unusual authentication patterns and data transfers to trusted cloud providers.
This campaign underscores the increasing sophistication of state-sponsored threat actors and their ability to adapt to defensive measures, making it clear that air-gapped networks require comprehensive security strategies that address both digital and physical attack vectors.
Comments
Please log in or register to join the discussion