Researchers discovered a critical remote code execution vulnerability in NGINX that has remained hidden for 18 years, affecting nearly a third of all websites globally. This finding raises profound questions about the security of foundational internet infrastructure and the effectiveness of traditional vulnerability detection methods.
In the intricate ecosystem of the modern internet, certain components stand as silent guardians, bearing the weight of global web traffic without fanfare. NGINX, the most popular web server today, powers approximately a third of all websites, serving as the critical edge between the public internet and countless backend systems. When a vulnerability of this magnitude emerges in such fundamental infrastructure, the implications ripple across the digital landscape.
The recent discovery of CVE-2026-42945, a critical remote code execution vulnerability affecting NGINX versions from 0.6.27 to 1.30.0, represents more than just another security advisory. It represents an 18-year blind spot in one of the internet's most widely deployed technologies, a period during which this vulnerability remained undetected despite countless security audits, code reviews, and penetration tests.
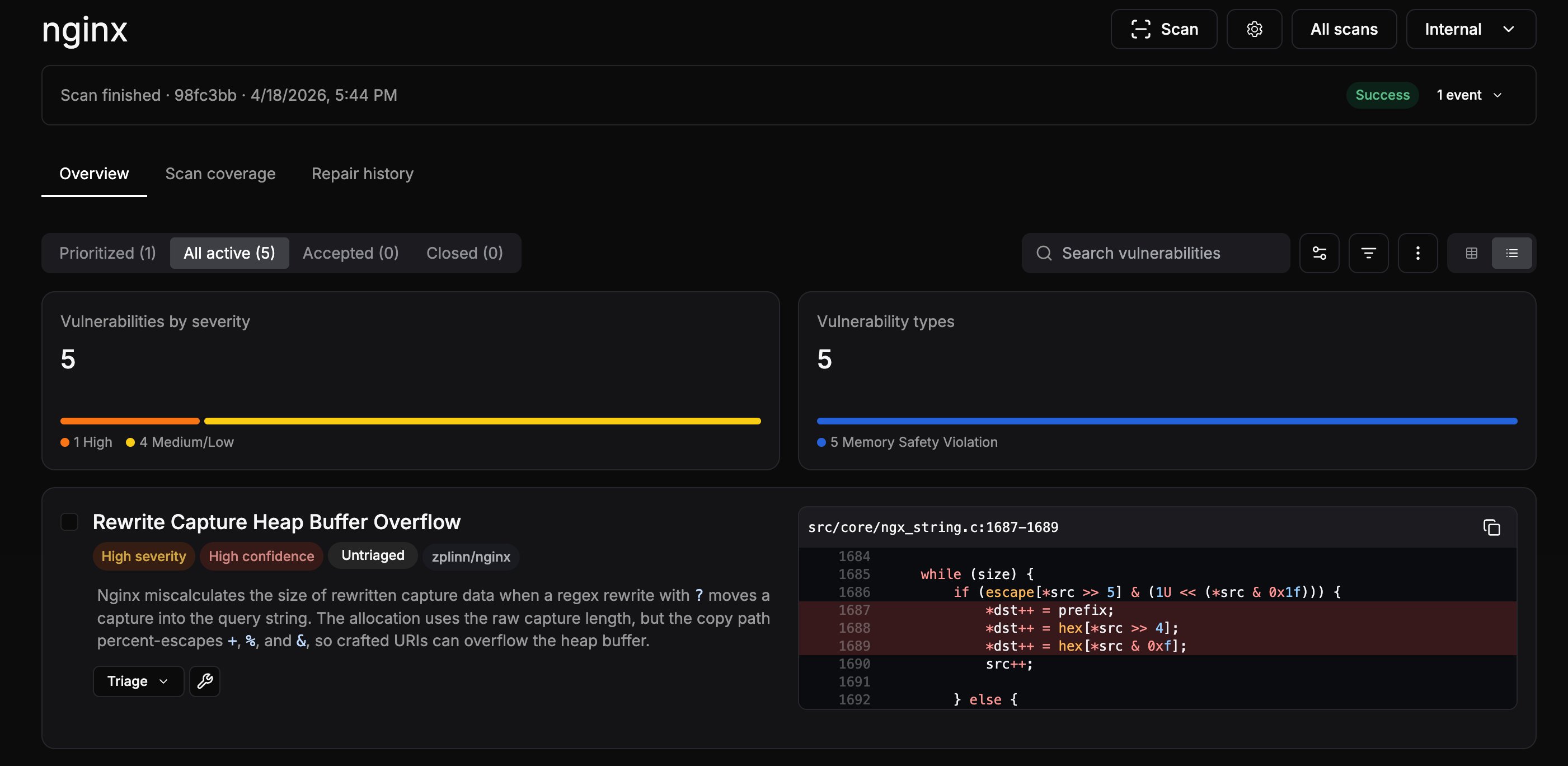
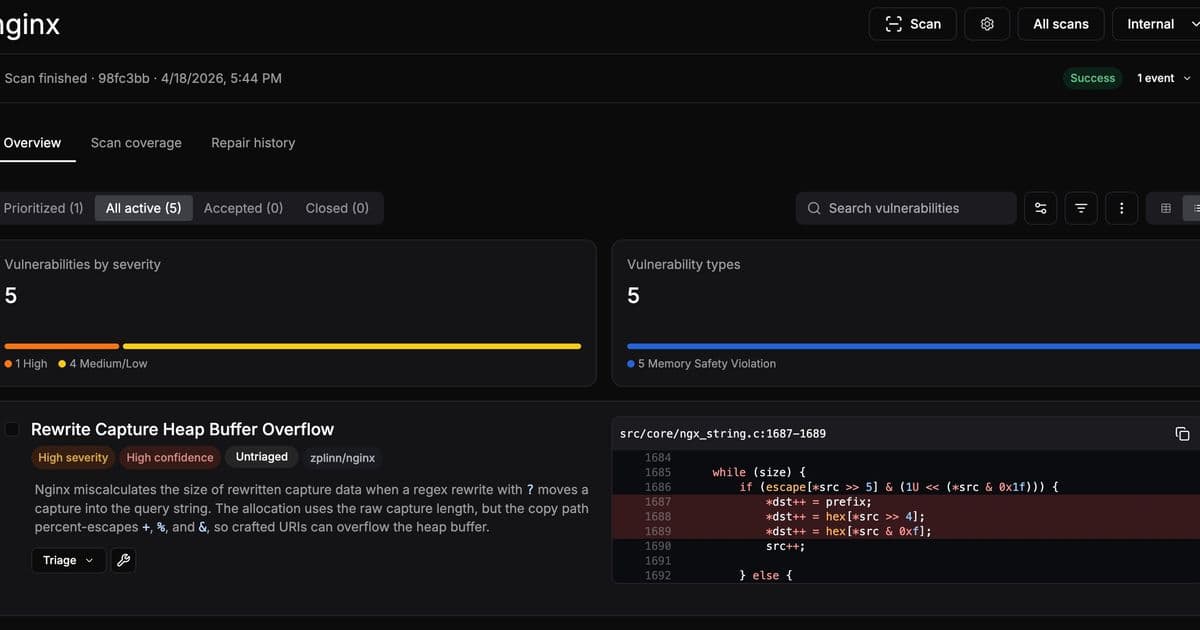
The researchers behind this discovery employed an autonomous analysis system called depthfirst to examine the NGINX source code. This approach represents a significant departure from traditional security testing methods. After six hours of scanning, the system identified five security issues, including the critical heap overflow in the ngx_http_rewrite_module that would later be confirmed by NGINX as CVE-2026-42945.
At the heart of this vulnerability lies a subtle flaw in NGINX's script engine, which processes configuration directives like rewrite and set. These directives are common building blocks in API gateway configurations, allowing developers to modify request paths and capture original request information. The vulnerability manifests specifically when a rewrite directive contains a question mark in its replacement string, followed by a set directive that references a regex capture group.
The technical intricacy of this flaw reveals the complexity of modern web server architecture. NGINX's script engine employs a two-pass process: first calculating the required memory length, then copying the actual data into the allocated buffer. This design optimizes performance by avoiding multiple small memory allocations. However, the vulnerability emerges from a state inconsistency between these two passes.
When a rewrite directive contains a question mark, the ngx_http_script_start_args_code function permanently sets the e->is_args = 1 flag on the script engine. This flag is never reset between script code evaluations. When a subsequent set directive references a regex capture group, it triggers the ngx_http_script_complex_value_code function, which uses a fresh, zeroed sub-engine for length calculation. Because this sub-engine has le.is_args = 0, the length calculation function does not account for URI escaping. During the second copy pass, however, the main engine still has e->is_args = 1, causing the copy function to apply URI escaping, which expands certain characters from one byte to three bytes. This mismatch between the calculated buffer size and the actual data written results in a heap buffer overflow.
{{IMAGE:2}}
The researchers developed a sophisticated exploitation technique that leverages NGINX's multi-process architecture. When a worker process crashes, the master process spawns a new one with an identical memory layout, allowing for repeated exploitation attempts without the memory layout changes that would typically complicate heap exploitation. The technique employs a cross-request heap feng shui approach, where the attacker precisely controls the heap layout and lifecycle of memory pools through connection ordering.
The implications of this discovery extend far beyond a single vulnerability. The fact that such a critical flaw remained hidden for 18 years suggests fundamental limitations in traditional security testing methodologies. Autonomous analysis systems, like the one used by the researchers, may represent a new frontier in vulnerability discovery, capable of identifying subtle flaws that human reviewers and automated testing tools might miss.
This vulnerability also highlights the critical importance of foundational internet infrastructure. NGINX sits at the edge of countless networks, processing requests that could originate from anywhere in the world. A single vulnerability in this core component can therefore expose entire backend systems to severe risks, potentially compromising not just individual websites but entire organizational infrastructures.
The affected versions list reveals the broad impact of this vulnerability, extending beyond NGINX Open Source to include various commercial products based on NGINX technology. This underscores the challenges of maintaining security in complex software ecosystems, where vulnerabilities in core components can have cascading effects across multiple products and platforms.
From a broader perspective, this discovery raises important questions about the security of open-source software. While the open-source model facilitates widespread scrutiny and collaboration, the sheer volume of code and the complexity of modern software systems can create blind spots that persist for years. The vulnerability in NGINX demonstrates that even widely used, well-maintained software can harbor critical flaws that evade detection through traditional means.
The timeline of the discovery and response process provides insight into the responsible disclosure practices in the security research community. The researchers identified the vulnerability on April 18, 2026, reported it to NGINX on April 21, and confirmed four of the five reported issues by April 24. By May 5, they had shared their proof of concept with NGINX, leading to the public advisory on May 13. This timeline reflects a coordinated effort to address the vulnerability before public disclosure, minimizing potential exposure while ensuring transparency.
The proof of concept developed by the researchers demonstrates unauthenticated remote code execution against NGINX via CVE-2026-42945. The source code is available on their GitHub repository, providing security professionals and system administrators with the tools needed to understand and test the vulnerability in controlled environments.
As organizations assess their exposure to this vulnerability, several factors must be considered. First, the vulnerability only affects configurations that use both rewrite and set directives with the specific pattern identified by the researchers. Second, the proof of concept requires ASLR to be disabled, which may not be the default configuration in all environments. However, the researchers note that NGINX's multi-process architecture could theoretically be leveraged to bypass ASLR, suggesting that the vulnerability might be exploitable in more environments than initially apparent.
The discovery of CVE-2026-42945 serves as a reminder that security is an ongoing process, not a destination. Even the most widely deployed software can harbor critical vulnerabilities, and new approaches to vulnerability discovery may be necessary to identify flaws that traditional methods miss. As the internet continues to evolve and become increasingly complex, the security of foundational components like web servers will remain a critical concern for organizations worldwide.
For those managing NGINX deployments, the immediate response should involve assessing whether their configurations use the vulnerable pattern and applying the necessary updates. The NGINX security advisory provides detailed information on affected versions and available patches. Beyond immediate remediation, organizations should consider the broader implications of this discovery, potentially reevaluating their security testing practices and exploring new approaches to vulnerability detection.
In the grand scheme of internet infrastructure, NGINX represents one of the silent pillars supporting the digital world. The discovery of an 18-year-old vulnerability in such critical software underscores the importance of continuous security vigilance and the need for innovative approaches to vulnerability discovery. As we navigate an increasingly complex digital landscape, the security of these foundational components will remain paramount to the stability and security of the internet as a whole.
Comments
Please log in or register to join the discussion