Security
Axios Security Check - Human Verification Required
2/1/2026
Security
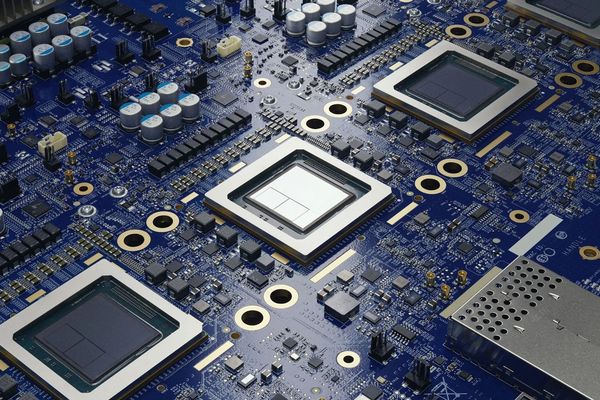
Former Google Engineer Convicted of Stealing AI Chip Trade Secrets for Chinese Interests
2/1/2026
Security
Reddit Blocks Developer Access: What It Means for API Users and the Developer Community
2/1/2026

Security
Microsoft confirms that a stack of bad Windows updates is causing boot issues
2/1/2026
Security
Reddit API Blocks Spark Developer Community Frustration
1/29/2026

Security
Amazon's AI Training Data Flagged for CSAM, But Source Remains Hidden
1/29/2026

Security
Survey of 100+ Energy Systems Reveals Critical OT Cybersecurity Gaps
1/29/2026

Security
From Triage to Threat Hunts: How AI Accelerates SecOps
1/29/2026
Security
Reddit Blocks Developer Access: Network Security Error Explained
1/29/2026
Security
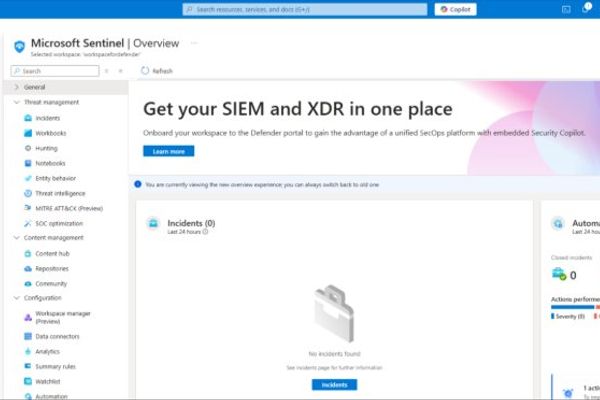
Microsoft Sentinel and Dataverse Integration: Unifying Security Monitoring for Power Platform
1/29/2026

Security
Saudi and Israeli Officials Visit D.C. to Discuss Possible U.S. Strikes on Iran
1/29/2026
Security
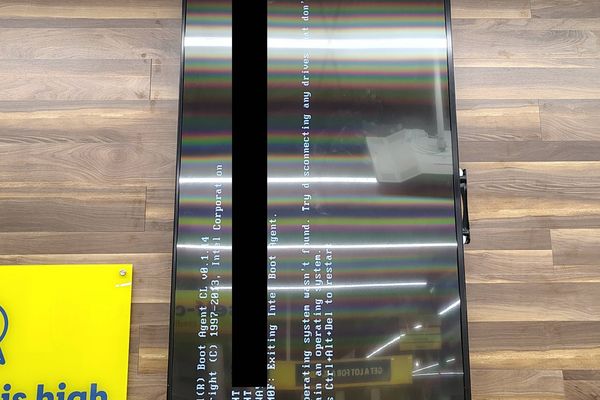
Lidl's Outdated Digital Signage Exposes Security Risks Amid Boot Failure
1/29/2026
Security
Reddit API Blocking Prompts Developer Backlash Over Access Issues
1/29/2026