
Security
New Verification Protocol Detects Malicious Code Generation in LLMs Without Execution
1/21/2026

Business
Johnson's Funding Strategy Aims to Avert Government Shutdown and Market Fallout
1/21/2026

Regulation
Chinese Researchers Develop CO₂-Based Lithium Recycling Method with Compliance Implications
1/21/2026

Regulation
Mozilla Expands Firefox Nightly Access with Native RPM Packages for Linux
1/21/2026
Dev
PowerToys v0.97.0 Overhauls Command Palette with Direct Utility Controls
1/21/2026

Startups
Applied Compute Valuation Reportedly Surges to $1.3B Amid Enterprise AI Customization Boom
1/21/2026

Security
Architecting Account Integrity: The Dual Authentication Design of Artemis
1/21/2026
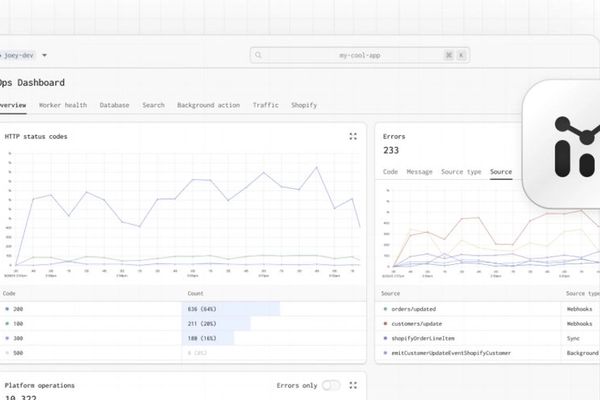
DevOps
Gadget's Operations Dashboard: Bridging the Gap Between Development and Production Monitoring
1/21/2026

Hardware
Mangmi Pocket Max: Modular Android handheld with high-refresh OLED display targets budget gamers
1/21/2026

Hardware
MorphoChrome: Democratizing Structural Color Fabrication with Handheld Light Programming
1/21/2026

Cybersecurity
VoidLink: First Advanced AI-Generated Malware Emerges from Cloud Shadows
1/21/2026

Regulation
Massachusetts Court Blocks Kalshi's Sports Betting Operation in Regulatory Showdown
1/21/2026
AI
Researchers Map AI Personas to Rein in Harmful 'Demon' Behaviors
1/21/2026