
Security
The Art of the Almost-Con: How Scammers Are Using Apple's Own Systems Against You
3/15/2026
Cybersecurity
The New York Times Website Experiences Major Outage Amid Cyber Attack Claims
3/14/2026

Security
Movies Featuring the Nmap Security Scanner
3/14/2026
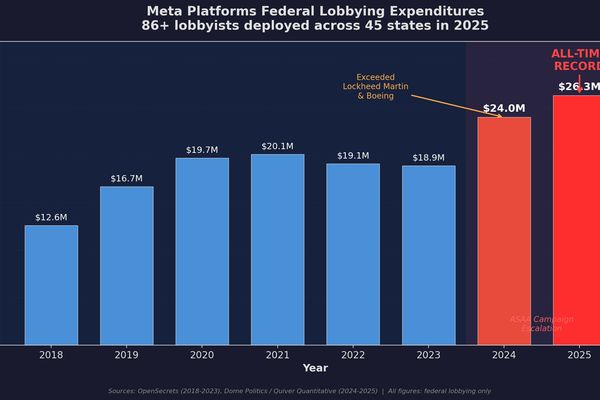
Regulation
Meta's $26.3M Lobbying Machine Shapes Age Verification Policy Across 45 States
3/14/2026

Cybersecurity
FBI Investigation Targets Malware-Infected Steam Games Stealing User Data and Cryptocurrency
3/14/2026
Security
Sweden's E-Government Platform Source Code Leaked in Major CGI Sverige Breach
3/13/2026

Security
Telus Digital Confirms Security Breach After ShinyHunters Claims 1PB Data Theft
3/13/2026

Regulation
Court Upholds Key Provisions of California's Online Child Safety Law
3/13/2026

Cybersecurity
AI agents can collaborate to bypass security controls and steal data
3/13/2026

Security
Iranian Hackers Wipe 200,000 Devices at Stryker in Major Cyberattack
3/13/2026

Cybersecurity
Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks
3/12/2026
Vulnerabilities
CISA Warns of Critical Vulnerabilities in Siemens Heliox EV Chargers
3/12/2026

Cloud
Microsoft Marketplace Expansion: March 2026 Brings 157 New Solutions for Cloud and AI Transformation
3/12/2026