Vulnerabilities
cPanel Urges Patching for Three Critical Vulnerabilities Enabling Code Execution and Privilege Escalation
5/9/2026
Security
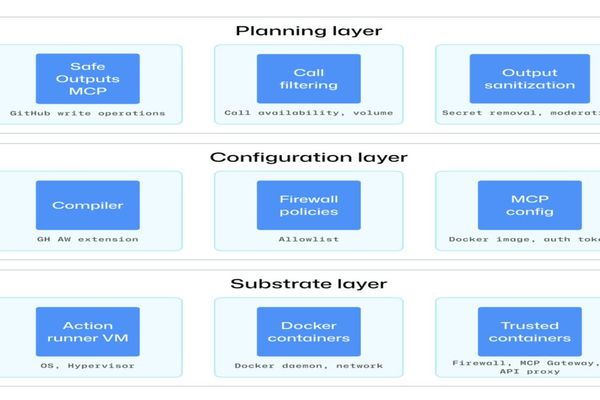
How GitHub Is Securing Agentic Workflows in Modern CI/CD Systems - InfoQ
5/8/2026
Security
Reddit's New Access Controls Spark Developer Concerns
5/8/2026

Security
ThreatsDay Bulletin: Edge Plaintext Passwords, ICS 0-Days, Patch-or-Die Alerts and 25+ New Stories
5/8/2026

Vulnerabilities
Mozilla says AI helped squash 423 Firefox security bugs
5/8/2026
Security
Linux Kernel Vulns and Supply Chain Risks Prompt Moratorium Warning for Rust Developers
5/7/2026
Vulnerabilities
Dirty Frag Linux Vulnerability Enables Root Access Across Major Distributions, No Patches Available
5/7/2026

Security
The Browser Is Breaking Your DLP: How Data Slips Past Modern Controls
5/7/2026
Security
Cloudflare Security Blocks: The Necessary Evil of Modern Web Protection
5/7/2026
Security
Securing the Untrusted Agentic Development Layer: Navigating AI Agent Risks in Software Development
5/7/2026
Vulnerabilities
Johnson Controls CEM AC2000 Security Vulnerabilities Prompt CISA Alert
5/6/2026
Vulnerabilities
CISA Adds Hitachi Energy PCM600 Vulnerabilities to KEV Catalog
5/6/2026
Vulnerabilities
Microsoft Releases Critical Security Update for Windows DNS Server Vulnerability
5/3/2026