A curated selection of the most compelling talks from the 39th Chaos Communication Congress, covering satellite data interception, zero-click exploits, CPU vulnerabilities, and the evolution of drone warfare.
The 39th Chaos Communication Congress (39C3) has once again proven to be a treasure trove of cutting-edge research and thought-provoking discussions in the world of technology and security. As the talks from this year's event become available, I found myself diving into the playlist, watching those presentations that immediately caught my attention. While there's immense value in exploring every talk, I wanted to share my personal highlights—the presentations that left me both fascinated and, at times, slightly unsettled by the implications of what I'd learned.
Harvesting Data from Satellites: The Sky Isn't the Limit
One of the most eye-opening talks I encountered was about using approximately $500 worth of equipment to eavesdrop on satellites belonging to military organizations, payment processors, and airline companies. The researchers demonstrated that with relatively modest investment, one could intercept data from satellites orbiting hundreds of miles above the Earth's surface.
The most shocking revelation wasn't just the accessibility of this technology, but the utter lack of basic security measures protecting sensitive data. Many military satellites were transmitting information in plain text, completely unencrypted. Even more baffling was the discovery that one military satellite was using what can only be described as a child's approach to security: simply shuffling strings like {military: true} to {imilatyr : rtue}.
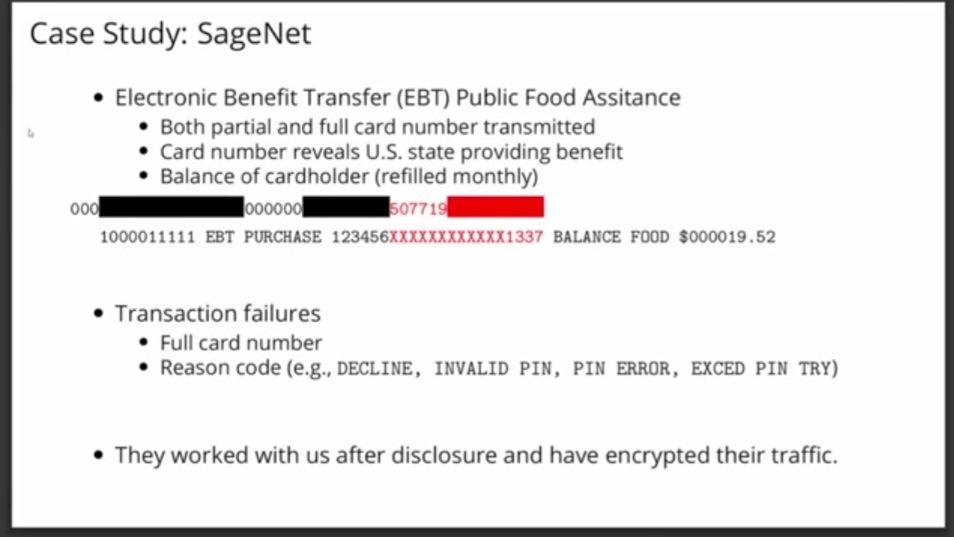
Slide From Talk: It turns out you could see unencrypted payment details (card numbers, card names and balances) of people when they use payment processors.
But perhaps the most concerning aspect was the ability to intercept unencrypted payment details—card numbers, cardholder names, and account balances—from people using payment processors. This isn't just a theoretical vulnerability; it's a real-world problem affecting actual financial transactions happening right now.
The Mechanics of 0-Click Exploits: Silent Invasion
Another fascinating presentation tackled a question that's been on many people's minds: how do 0-click exploits actually work? These are the attacks that can compromise your device without you ever clicking on a malicious link or opening a suspicious attachment.
The talk provided a step-by-step walkthrough of how hackers discover and weaponize these vulnerabilities, with practical demonstrations on WhatsApp and iMessage for both iOS and Samsung devices. What makes 0-click exploits particularly dangerous is their stealth—there's no phishing email to spot, no suspicious link to avoid. The compromise happens silently in the background while you're none the wiser.
CPUs Are Permanent Vulnerabilities: The Spectre Reality
Perhaps the most technically profound talk I watched was titled "Spectre in the real world: Leaking your private data from the cloud with CPU vulnerabilities." The speaker addressed a common criticism of transient execution CPU vulnerabilities like Spectre: while they're academically interesting, are they actually practical in real-world scenarios?
The answer, as demonstrated in this talk, is a resounding yes. Spectre operates at the CPU level, meaning software patches can't fully fix it—you'd need to replace the physical hardware. The speaker showed how, using these vulnerabilities, one could extract secrets from another virtual machine, provided both VMs reside on the same physical server. Critically, you don't even need access to the target VM; the attack works across virtual machine boundaries.
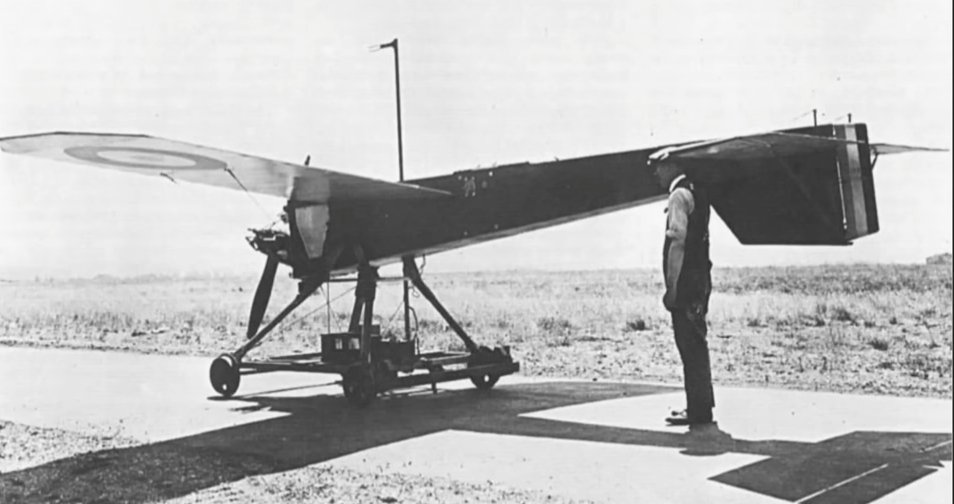
Slide From Talk: Remote control drone from 1930s
This demonstration makes a compelling case for why cloud users should consider dedicated servers over shared instances, despite the higher cost. The convenience of cheaper shared hosting comes with the hidden risk of side-channel attacks that can't be mitigated through conventional security measures.
The Current Drone Wars: A Historical Perspective
Stepping away from cybersecurity, I found a surprisingly enlightening talk about the use of drones in warfare. This presentation traced the historical evolution of military drones, revealing that their use in warfare dates back much further than most people realize—all the way to World War I, where they were initially used for information gathering.
The talk illustrated how drone technology has transformed from simple reconnaissance tools to sophisticated weapons systems, fundamentally changing the nature of modern warfare. Understanding this evolution provides crucial context for current geopolitical conflicts and the ethical debates surrounding autonomous weapons systems.
Why These Talks Matter
What makes these presentations from 39C3 so valuable isn't just the technical knowledge they impart, but the broader implications they reveal about our technological society. They expose the uncomfortable truth that many of our security assumptions are built on shaky foundations. Whether it's unencrypted satellite transmissions, silent 0-click exploits, hardware-level vulnerabilities that can't be patched, or the long history of autonomous weapons, these talks collectively paint a picture of a world where the line between science fiction and reality is increasingly blurred.
For anyone interested in technology, security, or simply understanding the hidden vulnerabilities in our interconnected world, these talks from 39C3 offer both education and a healthy dose of caution about the systems we increasingly depend upon.
Comments
Please log in or register to join the discussion