A sophisticated campaign has placed 26 malicious crypto wallet apps on Apple's App Store, targeting Chinese users with phishing schemes that steal recovery phrases and drain cryptocurrency assets.
A sophisticated campaign has placed 26 malicious crypto wallet apps on Apple's App Store, targeting Chinese users with phishing schemes that steal recovery phrases and drain cryptocurrency assets.
Fake wallets disguised as popular apps
The threat actors created apps impersonating well-known cryptocurrency wallets including Metamask, Coinbase, Trust Wallet, and OneKey. To avoid detection and circumvent restrictions on crypto apps in China, they disguised these malicious applications as games or calculator apps.
The campaign, dubbed FakeWallet by Kaspersky researchers, uses multiple deception techniques including typosquatting and fake branding to trick users into downloading what appears to be legitimate wallet software.
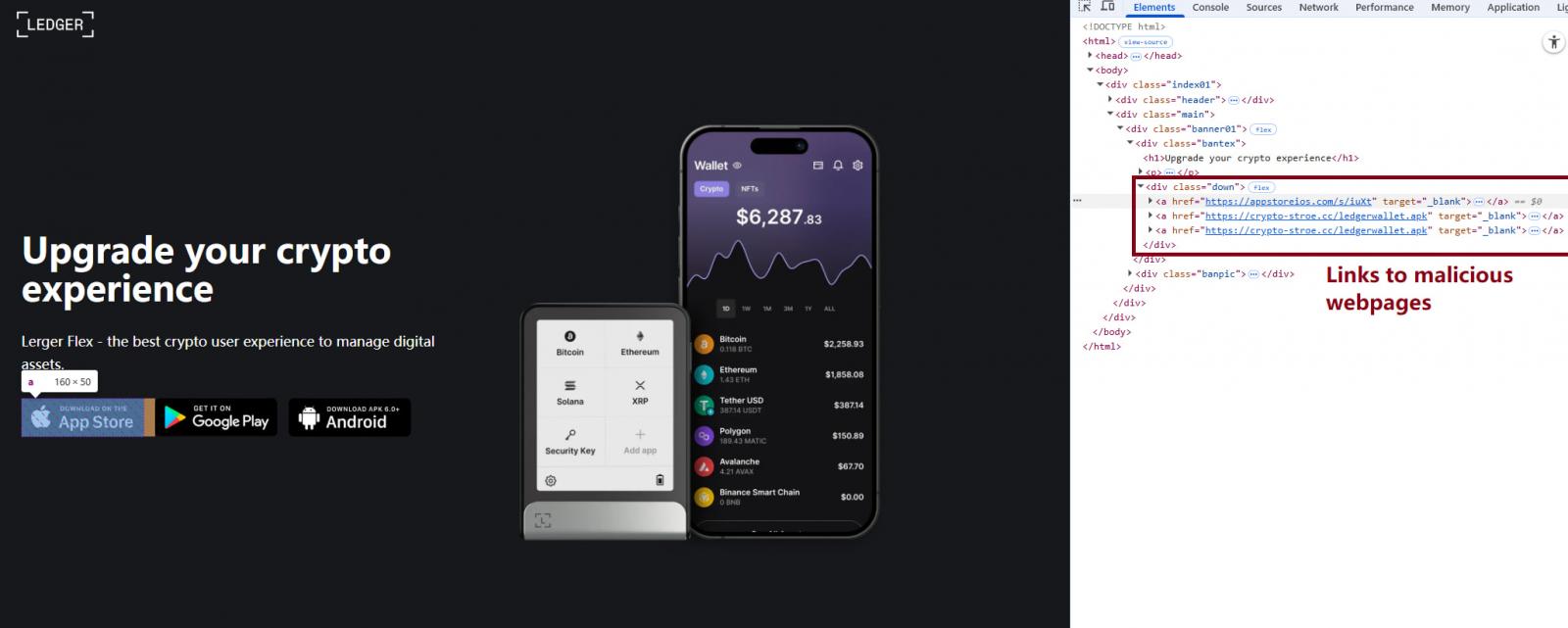
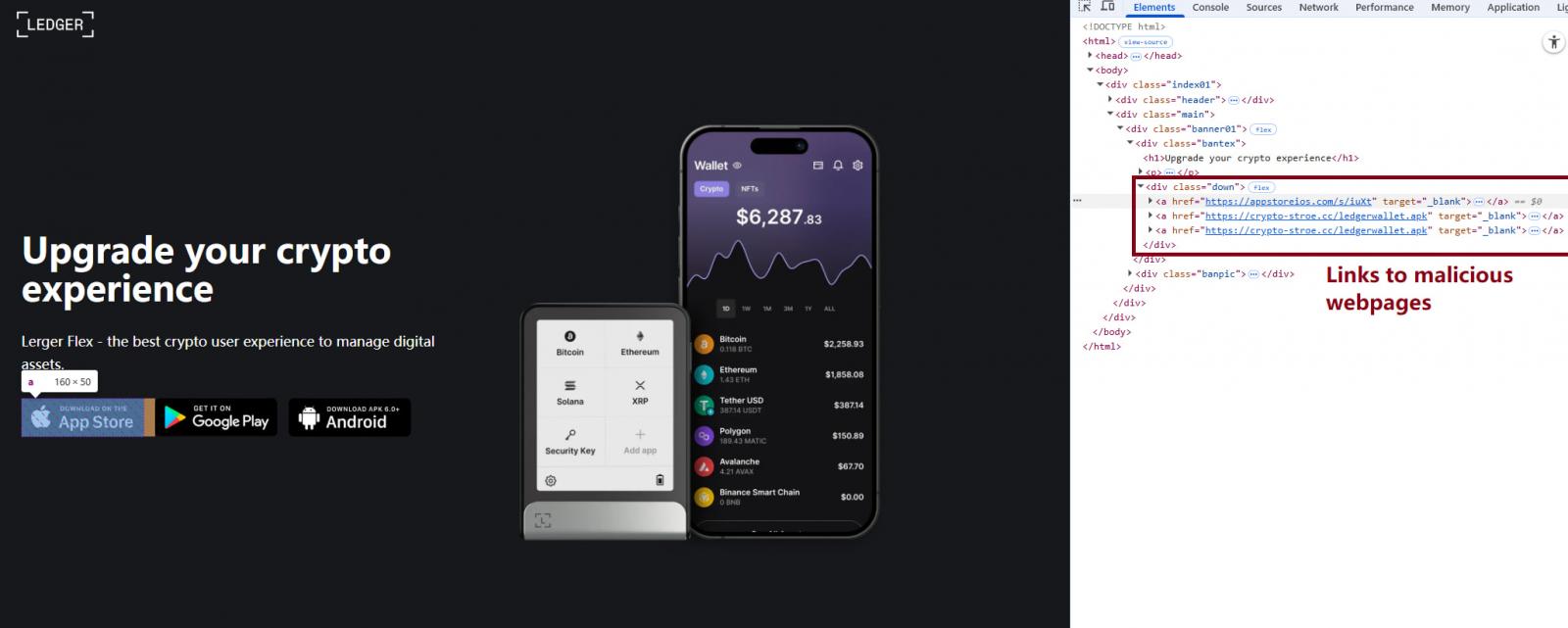 Fake website impersonating Ledger
Source: Kaspersky
Fake website impersonating Ledger
Source: Kaspersky
Multi-stage attack chain
Once installed, the apps redirect users to phishing pages designed to mimic legitimate cryptocurrency service portals. These sites then convince victims to download trojanized wallet applications using iOS provisioning profiles.
Provisioning profiles are legitimate enterprise features that allow sideloading of apps outside the App Store. The attackers abuse this mechanism to install malware directly onto devices, bypassing Apple's security review process.
 Installing a provisioning profile
Source: Kaspersky
Installing a provisioning profile
Source: Kaspersky
The trojanized apps contain malicious code that intercepts mnemonic phrases during wallet setup or recovery. These phrases are encrypted using RSA and Base64 encoding before being transmitted to the attackers.
For hardware wallet users, such as those with Ledger devices, the attackers employ in-app phishing prompts that display fake security verification screens. These prompts trick users into manually entering their seed phrases under the guise of legitimate security procedures.
Why seed phrases are so valuable
Seed phrases represent the ultimate key to cryptocurrency wallets. Unlike passwords or PINs, seed phrases are designed for wallet recovery and porting to new devices without requiring additional authentication. Once an attacker obtains a seed phrase, they can restore the victim's entire wallet on their own device and drain all funds without any possibility of recovery.
This makes seed phrase theft particularly devastating - there are no second factors, no recovery options, and no way to reverse the transaction once the cryptocurrency has been transferred.
Global implications despite Chinese focus
While Kaspersky notes that the campaign primarily targets users in China, the malware itself has no geographic restrictions. The operators could easily expand their targeting scope to affect users worldwide if they choose to do so.
The FakeWallet campaign appears connected to the SparkKitty operation that has been active since last year, suggesting an organized and persistent threat actor with significant resources.
Apple's response and security concerns
Apple has removed all 26 FakeWallet apps from the App Store following Kaspersky's responsible disclosure. However, the incident raises serious questions about Apple's app review process and how threat actors manage to bypass these security measures.
BleepingComputer has contacted Apple for comment regarding the threat actor's process to bypass App Store verifications but had not received a response at publication time.
This incident follows another high-profile case where a fraudulent Ledger app on Apple's App Store stole $9.5 million worth of cryptocurrency from 50 macOS users just last week.
Protection recommendations
Cryptocurrency holders should exercise extreme caution when downloading wallet applications, even from official app stores. Security experts recommend:
- Double-checking the publisher of any app before downloading
- Using only official links provided on the wallet provider's official website
- Being skeptical of apps that appear in unexpected categories (like games or calculators)
- Never entering seed phrases unless absolutely necessary and only in the official wallet application
- Using hardware wallets for significant cryptocurrency holdings
As cryptocurrency adoption continues to grow, attackers are increasingly targeting both the applications and the users themselves. This campaign demonstrates how threat actors are willing to invest significant effort in creating sophisticated, multi-stage attacks that exploit both technical vulnerabilities and human psychology.
The FakeWallet incident serves as a stark reminder that even official app stores can harbor malicious applications, and users must remain vigilant regardless of where they download software from.

Comments
Please log in or register to join the discussion