Google API keys previously considered harmless are now exposing sensitive Gemini AI data, with nearly 3,000 keys found publicly exposed online.
Researchers have discovered a critical security vulnerability affecting Google API keys that were previously considered harmless but now expose sensitive Gemini AI data. The issue affects thousands of organizations, including major financial institutions and even Google itself.

The Hidden Danger in Public Code
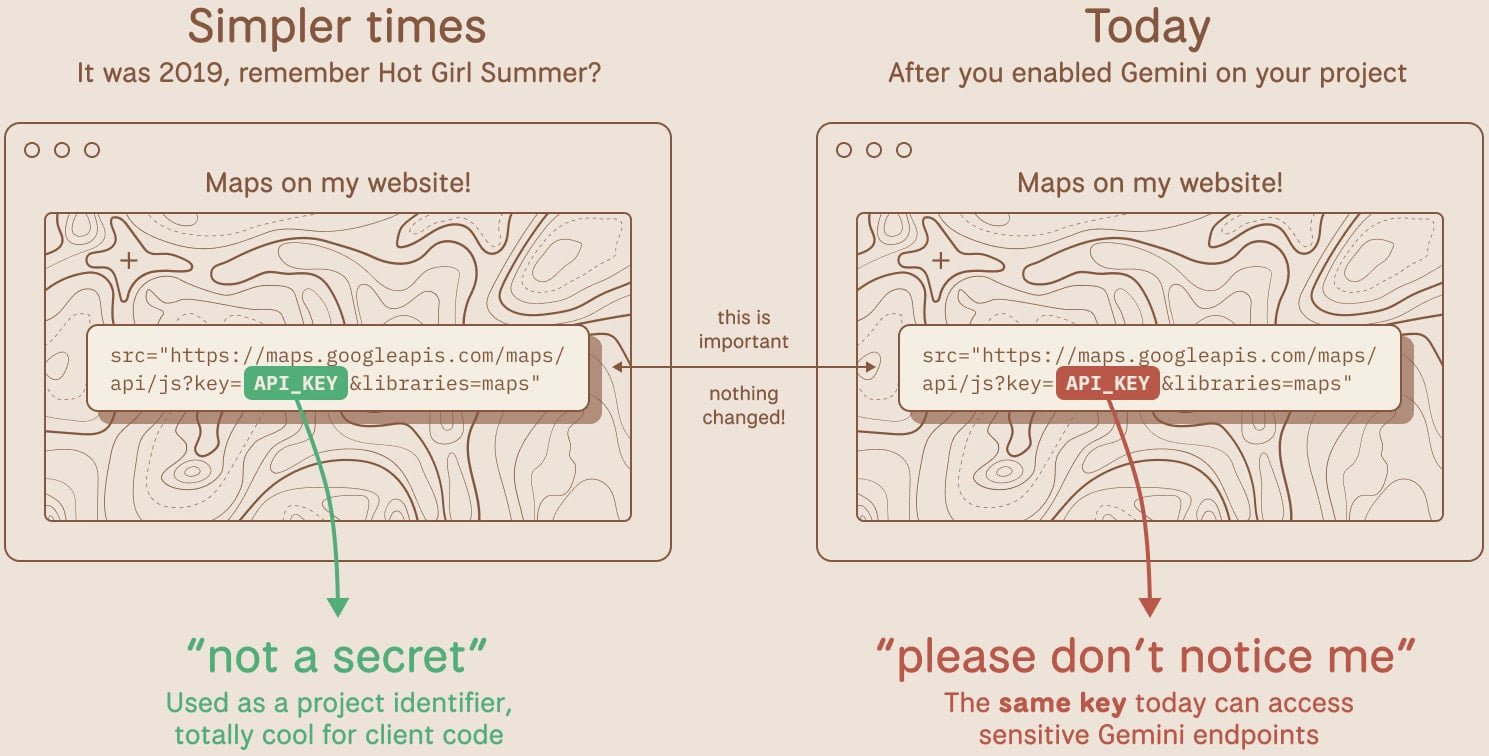
Google Cloud API keys have long been used by developers to extend website functionality - from embedding Google Maps to integrating YouTube videos and Firebase services. These keys were traditionally treated as non-sensitive identifiers that could safely be exposed in client-side code without risk.
However, everything changed with the introduction of Google's Gemini AI assistant. When developers began enabling the Gemini API in their projects, these same API keys suddenly gained the ability to authenticate to Google's AI services and access private data.
TruffleSecurity researchers discovered this vulnerability while scanning internet pages from organizations across various sectors. Their analysis of the November 2025 Common Crawl dataset revealed more than 2,800 live Google API keys publicly exposed in code.
How Attackers Can Exploit Exposed Keys
According to the researchers, attackers can simply copy an API key from a website's page source and use it to access private data through the Gemini API service. Since the Gemini API isn't free, attackers could potentially generate thousands of dollars in charges per day on a victim's account by making API calls for their benefit.
"Depending on the model and context window, a threat actor maxing out API calls could generate thousands of dollars in charges per day on a single victim account," Truffle Security warned.
Google's Own Keys Were Exposed
The vulnerability is particularly concerning because these API keys have been sitting exposed in public JavaScript code for years, suddenly gaining dangerous privileges without anyone noticing. In one striking example, researchers found an API key that had been deployed since at least February 2023 and was embedded in the page source of a Google product's public-facing website.
Google's Response and Mitigation Steps
After being informed of the issue on November 21, 2025, Google classified the flaw as "single-service privilege escalation" on January 13, 2026. The company has since implemented several protective measures:
- New AI Studio keys will default to Gemini-only scope
- Leaked API keys will be blocked from accessing Gemini
- Proactive notifications will be sent when leaks are detected
Google stated that it is "aware of the report and has worked with the researchers to address the issue."
What Developers Should Do Now
Developers are urged to take immediate action to protect their systems:
- Audit all API keys in their environment to identify any that are publicly exposed
- Rotate exposed keys immediately to prevent unauthorized access
- Check if Gemini (Generative Language API) is enabled on their projects
- Use detection tools like TruffleHog, an open-source tool that can detect live, exposed keys in code and repositories
This vulnerability highlights the evolving security landscape as AI services become more integrated into development workflows. What was once considered safe practice - exposing API keys in client-side code - has become a significant security risk.
The discovery serves as a reminder that security practices must evolve alongside technological changes. Developers should regularly review their security assumptions and update their practices as new services and capabilities are introduced to platforms they use.

Comments
Please log in or register to join the discussion