Microsoft Entra is getting native backup functionality, as revealed by new Graph API roles, potentially solving the long-standing challenge of restoring deleted directory objects with their original IDs.
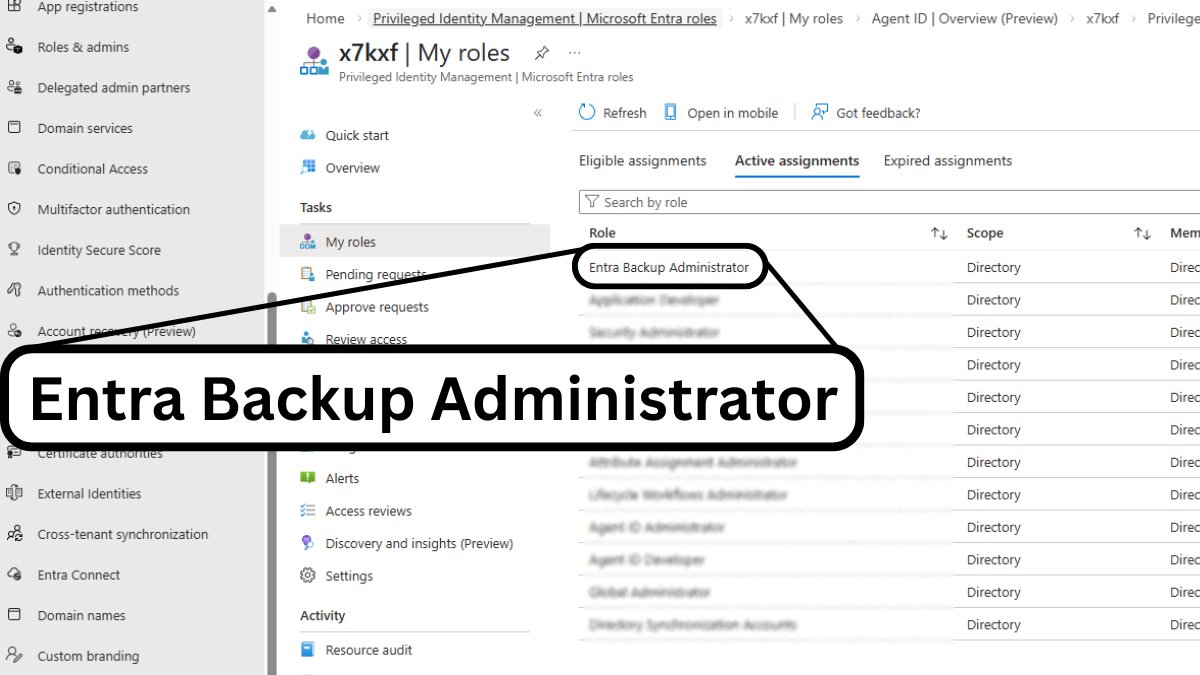
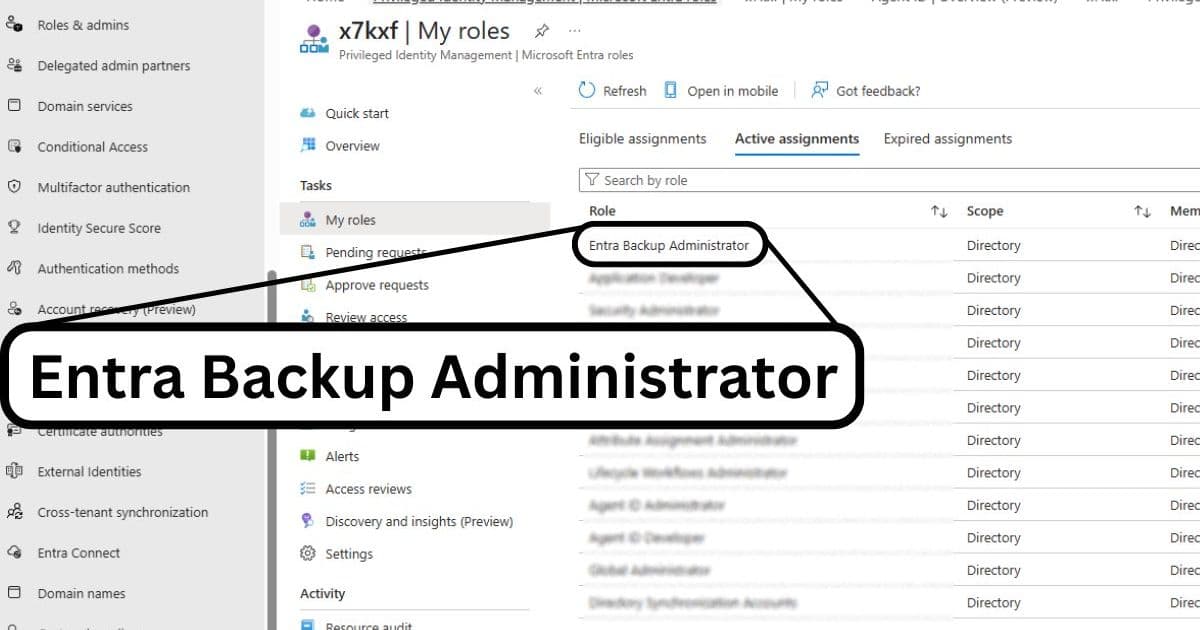
Microsoft Entra is set to receive native backup capabilities, as evidenced by the recent discovery of two new roles in the Graph API: Entra Backup Reader and Entra Backup Administrator. This development marks a significant shift in how organizations can protect and recover their Entra configurations, addressing a long-standing gap in Microsoft's identity and access management ecosystem.
The Current State of Entra Backup Solutions
Today, protecting your Entra tenant configuration is largely a DIY project. Most organizations rely on third-party tools like Entra Exporter to dump configurations into JSON files, or turn to paid solutions from vendors such as Veeam or AvePoint. While these tools are effective, they come with inherent limitations. The most significant challenge is the lack of a native "undo" button for many Entra objects. When third-party tools restore deleted objects, they often have to recreate them from scratch, resulting in new Object IDs and extensive manual work to re-link applications and policies.
This fragmented approach becomes even more problematic with the release of Unified Tenant Configuration Management, which centralizes more Entra settings but still lacks native backup functionality. The absence of a first-party recovery solution has been a notable gap in Microsoft's identity management portfolio.
The New Entra Backup Roles
The discovery of these new roles provides the clearest evidence yet that a first-party recovery solution is imminent. When examining the role definitions in the Graph API, we can see detailed permissions that point to a comprehensive backup solution:
Entra Backup Administrator (ID: b6a27b2b-f905-4b2e-81b5-0d90e0ef1fdb)
- Manage all aspects of Microsoft Entra Backup
- Create recovery jobs and manage backup snapshots
- Permissions include:
microsoft.directory/backup/preview/cancel,microsoft.directory/backup/preview/create,microsoft.directory/backup/recovery/cancel,microsoft.directory/backup/recovery/create,microsoft.directory/backup/standard/read
Entra Backup Reader (ID: f42252d9-5400-4d7b-b9ef-cc582dbb8577)
- Read all aspects of Microsoft Entra Backup
- List preview jobs, recovery jobs, and backup snapshots
- Create preview jobs
- Permissions include:
microsoft.directory/backup/preview/cancel,microsoft.directory/backup/preview/create,microsoft.directory/backup/standard/read
Interestingly, these roles can be assigned to user accounts today through PowerShell, though the associated UX features appear to be behind a service-side tenant whitelist. The roles don't currently impact service usage or appear in the Entra UX, but they are visible when exporting role assignments via the portal.
Why Native Backup Matters
A native, first-party backup solution represents a massive win for several compelling reasons:
Integration Benefits: By keeping backup functionality within the Entra ecosystem, Microsoft can likely handle the restoration of underlying metadata far more effectively than external tools. This includes preserving original Object IDs, which has been a persistent pain point when restoring from third-party backups.
Security Considerations: In scenarios where your environment might be compromised, having a native backup solution provides an additional layer of protection. However, organizations should still consider air-gapped solutions for critical configuration backups, especially in high-security environments.
Tenant Recovery Scenarios: While rare, situations requiring restoration into a brand-new tenant become significantly more manageable with native backup capabilities. This is particularly relevant for external tenants that rely solely on Entra capabilities.
What This Means for Organizations
The introduction of native Entra backup capabilities will fundamentally change how organizations approach identity management resilience. Rather than stitching together multiple third-party solutions, IT teams will have a unified, Microsoft-supported approach to protecting their directory configurations.
This development also aligns with broader industry trends toward integrated security and management solutions. As organizations increasingly rely on cloud-based identity services, having native backup and recovery capabilities becomes essential for business continuity and disaster recovery planning.
While Microsoft hasn't officially announced this feature yet, the presence of these roles in the Graph API strongly suggests that a first-party backup solution is on the horizon. Organizations should monitor official Microsoft communications for announcements regarding availability and implementation details.
For now, those relying on third-party backup solutions can take comfort in knowing that a more integrated approach is coming, though the timeline for general availability remains unclear. The question isn't if Microsoft will provide native Entra backup capabilities, but rather when these features will become widely available to tenants.
Comments
Please log in or register to join the discussion