Chinese-linked AI security tool CyberStrikeAI found driving global FortiGate compromise campaign
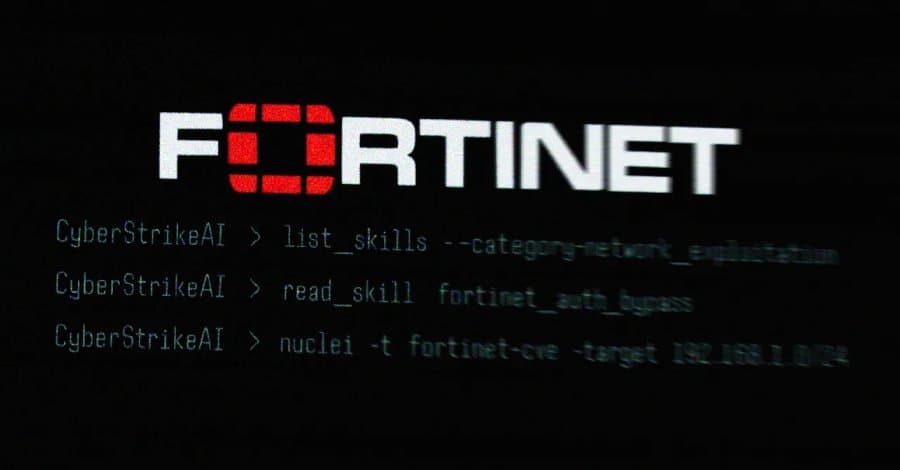
An open-source AI security tool called CyberStrikeAI has been identified as the primary weapon behind a sophisticated campaign that compromised over 600 Fortinet FortiGate appliances across 55 countries. The discovery, made by security researchers at Team Cymru, reveals how freely available offensive security tools are being weaponized at scale.

The campaign came to light when Amazon Threat Intelligence detected systematic targeting of FortiGate devices using generative AI services like Anthropic Claude and DeepSeek. What researchers found was even more concerning: the attacks were powered by CyberStrikeAI, an AI-native security testing platform built in Go that integrates more than 100 security tools for vulnerability discovery, attack-chain analysis, and result visualization.
Chinese Developer with Government Ties
The tool was created by a developer operating under the alias Ed1s0nZ, described as China-based with "some ties to the Chinese government." Team Cymru observed 21 unique IP addresses running CyberStrikeAI between January 20 and February 26, 2026, with servers primarily hosted in China, Singapore, and Hong Kong, though additional servers were detected in the U.S., Japan, and Switzerland.
Ed1s0nZ's GitHub profile reveals a pattern of developing tools that blur the line between security research and offensive capabilities. Beyond CyberStrikeAI, the developer has published:
- watermark-tool: Adds invisible digital watermarks to documents
- banana_blackmail: A Golang-based ransomware tool
- PrivHunterAI: Uses AI models to detect privilege escalation vulnerabilities
- ChatGPTJailbreak: Contains prompts to jailbreak OpenAI models
- InfiltrateX: A scanner for privilege escalation vulnerabilities
- VigilantEye: Monitors databases for sensitive information disclosure
State-Aligned Cyber Contractor Connections
Security researcher Will Thomas (@BushidoToken) noted that Ed1s0nZ's GitHub activities indicate interactions with organizations supporting potentially Chinese government state-sponsored cyber operations. This includes Chinese private sector firms with known ties to the Ministry of State Security (MSS).
One such company is Knownsec 404, a Chinese security vendor that suffered a major leak of over 12,000 internal documents. The leak exposed the firm's government clientele, hacking tools, stolen data from South Korean call logs and Taiwanese critical infrastructure, and ongoing cyber operations targeting other countries.
DomainTools described Knownsec as a "state-aligned cyber contractor" capable of supporting Chinese national security, intelligence, and military objectives. The company maintains tools like ZoomEye and the Critical Infrastructure Target Library, providing China with a global reconnaissance system cataloging millions of foreign IPs, domains, and organizations.
Vulnerability Database Connections
Further investigation revealed that Ed1s0nZ had previously been honored with the Level 2 Contribution Award to the China National Vulnerability Database of Information Security (CNNVD). The developer has since attempted to remove references to this award from their GitHub profile, suggesting an active effort to obscure state ties.
According to research by Bitsight, China maintains two different vulnerability databases: CNNVD (overseen by the Ministry of State Security) and CNVD (controlled by CNCERT). Recorded Future has found that CNNVD takes longer to publish vulnerabilities with higher CVSS scores than those with lower ones, potentially giving Chinese actors a window of opportunity.
Implications for AI-Powered Security Tools
The adoption of CyberStrikeAI represents a concerning evolution in the proliferation of AI-augmented offensive security tools. What was designed as an open-source security testing platform has been repurposed for large-scale attacks, demonstrating how freely available AI tools can be weaponized by threat actors.
The campaign's scale - compromising 600+ devices across 55 countries - shows that AI-powered security tools are no longer theoretical threats but practical weapons in the hands of sophisticated attackers. The use of generative AI services like Claude and DeepSeek to assist in the attacks also highlights how legitimate AI services can be abused for malicious purposes.
As AI security tools become more sophisticated and accessible, organizations must prepare for a new era where automated, intelligent attacks can be launched at unprecedented scale and speed. The line between security research and offensive capabilities continues to blur, creating new challenges for defenders worldwide.
For organizations running Fortinet FortiGate appliances, this campaign underscores the critical importance of keeping firmware updated and monitoring for unusual network activity. The attackers exploited vulnerabilities in widely deployed network security devices, turning the very tools meant to protect networks into entry points for compromise.
Comments
Please log in or register to join the discussion