Vercel discloses security incident affecting limited customers after threat actors claim to have breached systems and are selling stolen data including employee information and internal access.
Vercel has confirmed a security breach affecting a limited subset of customers after threat actors claimed to have compromised the cloud development platform and are attempting to sell stolen data on hacking forums.

The Breach Timeline
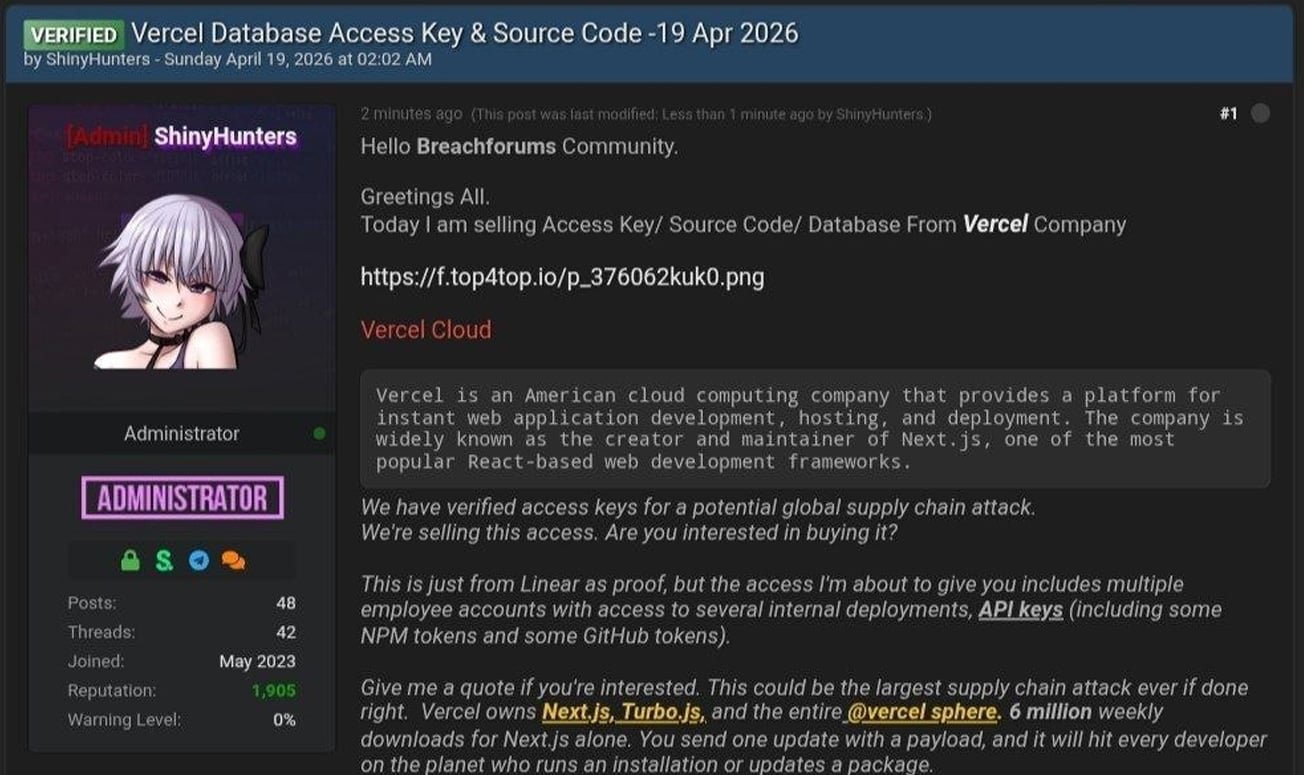
The incident came to light when a threat actor claiming affiliation with the ShinyHunters group posted on a hacking forum that they had breached Vercel's systems. The attacker claimed to possess access keys, source code, database data, and internal deployment credentials.
Vercel published a security bulletin acknowledging the unauthorized access to internal systems, stating that while services remained operational, they were actively investigating the incident and had engaged external incident response experts.
How the Attack Occurred
In subsequent updates, Vercel revealed the breach originated from a compromised third-party AI tool's Google Workspace OAuth application. The attack chain began when a Vercel employee's Google Workspace account was compromised through a breach at Context.ai, an AI platform.
From there, the attacker escalated privileges into Vercel environments, accessing environment variables that were not marked as sensitive. While Vercel stores all customer environment variables fully encrypted at rest, variables designated as "non-sensitive" were not encrypted, allowing the attacker to enumerate and gain further access.
Data Exposure Details
The threat actor shared several pieces of evidence on Telegram:
- A text file containing 580 employee records with names, Vercel email addresses, account status, and activity timestamps
- A screenshot of what appears to be an internal Vercel Enterprise dashboard
- Claims of access to Linear (project management tool) data, internal deployments, and various API keys including NPM and GitHub tokens
The attacker also claimed to be in contact with Vercel regarding a $2 million ransom demand, though this has not been independently verified.
Customer Impact and Mitigation
Vercel has advised affected customers to:
- Review environment variables for sensitive information
- Use the sensitive environment variable feature to ensure encryption at rest
- Rotate secrets if necessary
The company has implemented dashboard updates including an overview page for environment variables and improved interfaces for managing sensitive variables.
Security Implications
This incident highlights the risks associated with third-party OAuth integrations and the importance of proper environment variable management. Even with encryption at rest, improperly classified variables can create significant security gaps.
Vercel's investigation confirmed that its open-source projects, including Next.js and Turbopack, remain secure and unaffected by the breach.
Industry Context
The Vercel breach follows a pattern of recent high-profile security incidents affecting major tech companies. Similar attacks have targeted platforms like McGraw-Hill (13.5 million accounts affected), Rockstar Games, and Hims & Hers, demonstrating the ongoing challenges in securing cloud infrastructure and third-party integrations.
What This Means for Developers
For developers using Vercel or similar platforms, this incident serves as a reminder to:
- Regularly audit and classify environment variables
- Enable encryption for all sensitive data
- Monitor third-party OAuth application permissions
- Implement defense-in-depth strategies beyond basic encryption
Vercel continues to investigate the full scope of the breach and has notified law enforcement. The company promises to update its security bulletin as the investigation progresses.


Comments
Please log in or register to join the discussion