
Vulnerabilities
Broken VECT 2.0 Ransomware Flaw Turns Encryption Tool into Data Wiper
4/29/2026
Security
Critical: Microsoft Security Update Protocol for Organizations
4/29/2026
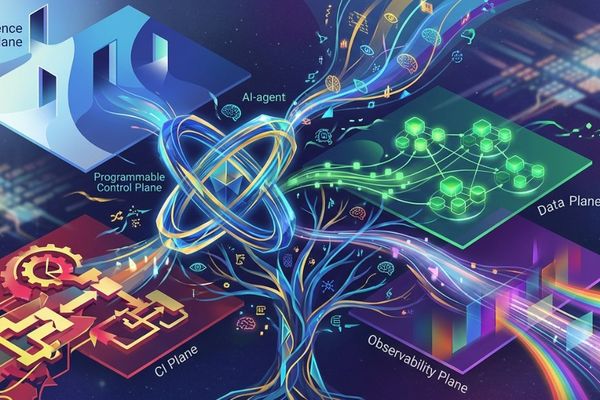
Infrastructure
OpenChoreo 1.0 Emerges as Kubernetes IDP with AI Integration and GitOps Foundation
4/29/2026
Regulation
Week-Long Outage: Lifelong Lessons - Building Resilience Through Experience
4/29/2026

Smartphones
Motorola Razr 70 Plus Leaks with Official Renders, Global Expansion Confirmed
4/29/2026

AI
Parallel Web Systems Raises $100M at $2B Valuation, Betting on AI Agent Search
4/29/2026
DevOps
We Upgraded to a Frontier Model and Our Costs Went Down
4/29/2026

AI
Musk vs. Altman: The Unseen Battle for AI Supremacy
4/29/2026

Regulation
Judge Denies Sam Bankman-Fried's Request for New Trial Despite 'New Evidence'
4/29/2026

LLMs
Evaluating and Optimizing LLM Performance: A Practical Guide
4/29/2026

Hardware
GPD BOX: Panther Lake Mini PC with Revolutionary MCIO 8i Port for External PCIe 5.0 Connectivity
4/29/2026

Infrastructure
GitHub Leverages eBPF to Enhance Deployment Safety and Prevent Circular Failure Dependencies
4/29/2026
Security
NSA GRASSMARLIN and CISA Offer Critical Cybersecurity Resources Amid Federal Funding Uncertainty
4/29/2026