
Security
When Sysadmins Ruled the Earth: A Post-Apocalyptic Network Survival Story
1/18/2026

Security
GhostPoster Campaign Resurfaces with 17 Malicious Browser Extensions
1/18/2026

Regulation
Every data centre is a U.S. military base: The hidden costs of digital dependence
1/17/2026

Privacy
The Untouchable Hacker God: Inside Finland's Largest Data Breach
1/17/2026

Security
Trump and Netanyahu's Iran Discussion Signals Shift in U.S.-Israel Strategic Alignment
1/17/2026

Regulation
California's Attorney General Targets xAI Over Non-Consensual Image Generation
1/17/2026

Vulnerabilities
Researchers Hijack StealC Malware Control Panel Through XSS Flaw, Exposing Operator Details
1/16/2026

Business
Exclusive: Global trust data finds our shared reality is collapsing
1/16/2026

Security
Chinese Spies Exploit Maduro Capture in Sophisticated Phishing Campaign Targeting US Agencies
1/15/2026

Security
Security Party: A Gathering for Tech Workers to Reclaim Digital Safety
1/15/2026
Security
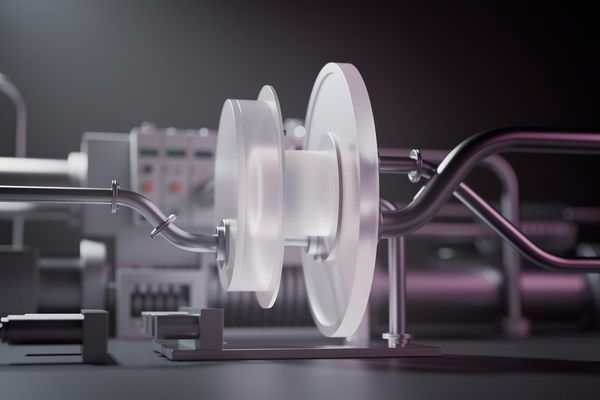
CISA and AVEVA Partner to Enhance Process Optimization Security in Critical Infrastructure
1/15/2026

Cybersecurity
US Cyberattack in Caracas Reveals Offensive Capabilities, Prompting Senate Scrutiny
1/15/2026

Regulation
The Pirate Sports Streaming Ecosystem: A 1.6B-View Machine Powered by Unlicensed Gambling Ads
1/15/2026