
DevOps
Architectural Governance at AI Speed: Declarative Architecture for the GenAI Era
3/27/2026
DevOps
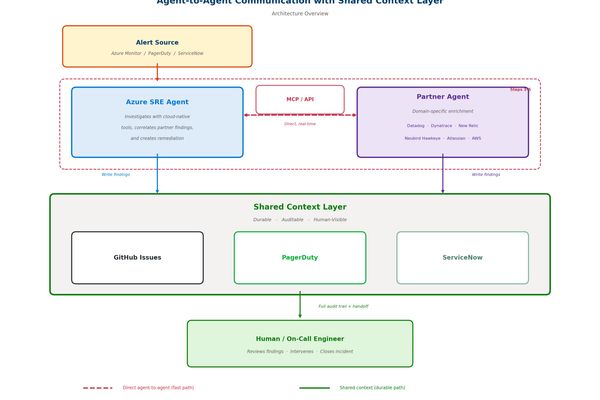
Shared Agent Context: How Microsoft Tackles Partner Agent Collaboration in Azure SRE
3/26/2026

DevOps
The Hidden Complexity of Modern DevOps Roles: Beyond the Salary Tags
3/23/2026

DevOps
AI Is Amplifying Software Engineering Performance, Says the 2025 DORA Report
3/17/2026

Cloud
Azure Front Door Resiliency: Architecting for Mission-Critical Workloads
3/17/2026

DevOps
GitHub Actions: Democratizing CI/CD for Every Developer
3/16/2026
Infrastructure
Brilliant backups landed web developer in big trouble • The Register
3/16/2026
Cloud
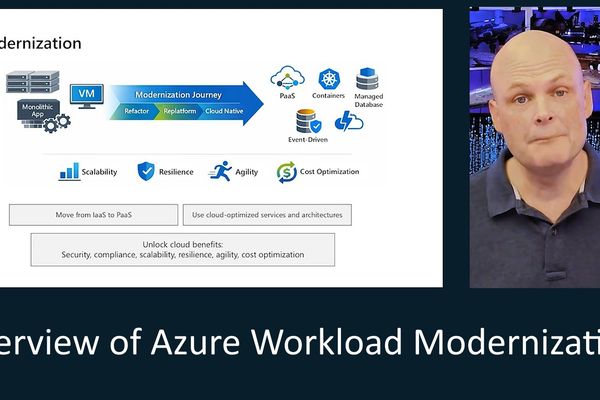
Azure Workload Modernization: From VMs to Cloud-Native Architecture
3/16/2026
Infrastructure
MySQL Too many connections: How I Debugged It and Scaled the Connection Pool
3/16/2026
AI
The AI-Powered Linux Setup: Trading Mastery for Efficiency
3/15/2026

Backend
Scaling Your FastAPI Project: From Simple API to Feature-Rich User Platform
3/14/2026
Infrastructure
Building Developer Tools That Scale: Lessons from Email Infrastructure
3/13/2026

Infrastructure
Membangun Dashboard Operasional ISP: Dari Monitoring Jaringan hingga Tiket Gangguan
3/13/2026