A deep dive into building a digital signature microservice with Go, gRPC, and cryptographic infrastructure, exploring performance, security, and architectural trade-offs.
In the world of financial technology, where milliseconds matter and security is non-negotiable, building systems that can process sensitive documents at scale presents unique challenges. Over the past two weeks, I tackled an intensive technical challenge: developing a digital signature microservice using Go and gRPC that would push me far beyond typical business logic into the realm of infrastructure engineering and cryptography.
The Technical Challenge
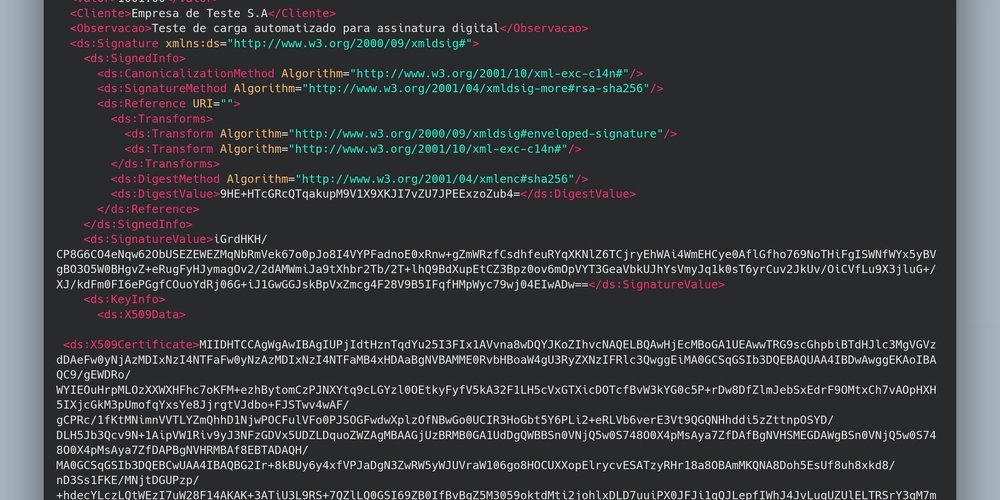
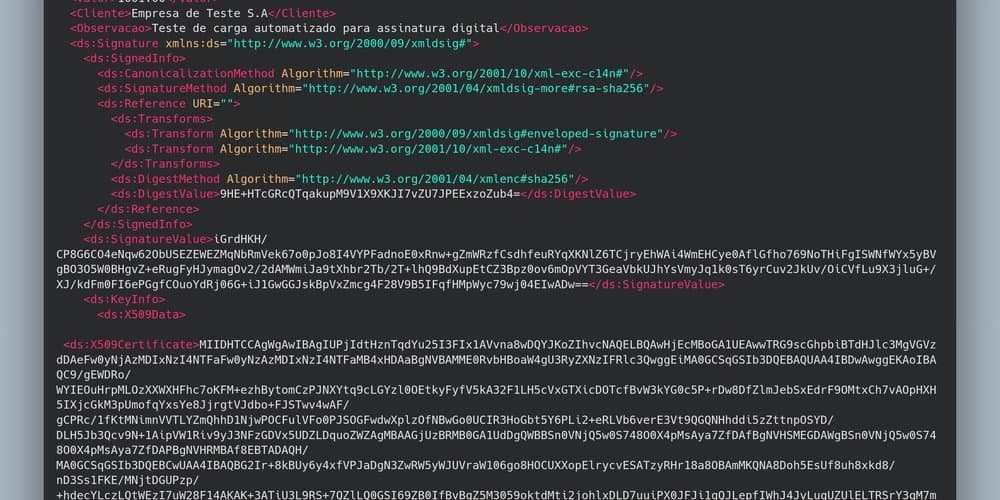
The objective was clear but demanding: create a processing engine capable of receiving financial documents in XML format, parsing them, ensuring integrity through digital signature algorithms, and returning uniquely signed documents. All of this needed to happen with a relentless focus on high performance and availability.
This wasn't just another CRUD application. This was about building infrastructure that financial institutions could trust with their most sensitive documents.
Engineering Stack Selection
For such complexity, the technology stack had to be equally robust:
Go & gRPC: The choice was driven by the need for low latency and efficient machine-to-machine communication. By avoiding the overhead of JSON/REST, we could achieve the performance characteristics required for high-throughput document processing.
HashiCorp Vault: Secure secret management became critical for handling private keys. Vault provided the cryptographic operations and secure storage needed to protect sensitive credentials.
MinIO: Object storage for certificate files (.pfx) offered a scalable, S3-compatible solution that could grow with demand.
MySQL & Redis: This combination provided metadata persistence with Redis serving as a caching layer to optimize query performance.
X.509 Cryptography: The logic for extracting metadata and validating trust chains formed the backbone of our security model.
Implementation Highlights
The architecture was deliberately designed around two fundamental pillars: idempotency and security at rest. These aren't just nice-to-have features when dealing with financial documents—they're absolute requirements.
Multi-Tenant Security
One of the most critical design decisions was implementing true multi-tenant isolation. Each consumer manages their own certificate, completely isolated and protected through Vault's encryption. This approach ensures that even if one tenant's data were compromised, others remain secure.
Performance Through Protocol Choice
By foregoing a graphical interface and focusing purely on heavy processing, gRPC proved its worth. Multiple systems could simultaneously consume the service with remarkable stability. The binary protocol and HTTP/2 multiplexing meant we could handle concurrent requests without the serialization overhead that plagues traditional REST APIs.
Culture of Testing
To validate resilience, I developed automation scripts in Bash and leveraged grpcurl for stress testing. These tools allowed us to simulate multiple clients simultaneously, revealing bottlenecks and ensuring the system could handle real-world load patterns.
Key Learnings
The practical conclusion is clear: gRPC is the excellence choice for system integration where stability and heavy processing are non-negotiable. When you need to move beyond simple request-response patterns into true high-performance computing, the protocol's advantages become undeniable.
Working with cryptography and digital certificates is complex, but deeply rewarding. There's something uniquely satisfying about seeing performance validations prove out in practice—knowing that your system can handle the demands of global-scale operations.
This project represents more than just another technical achievement. It's knowledge acquired and ready for application in solutions that operate at global scale. In an era where digital trust is paramount, building systems that can securely and efficiently process sensitive documents isn't just valuable—it's essential.
The journey from concept to production-ready microservice reinforced a fundamental truth: in high-stakes domains like financial technology, the right architectural choices, combined with appropriate technology selection, can transform seemingly impossible requirements into achievable reality.
Comments
Please log in or register to join the discussion