Security researchers at Huntress Labs uncovered a sophisticated ransomware ecosystem after investigating what appeared to be a standard brute force attack on an exposed RDP server, revealing geo-distributed infrastructure and a shady VPN service used by initial access brokers.
What started as another routine brute-force alert on an exposed Remote Desktop Protocol (RDP) server unexpectedly unraveled a complex ransomware-as-a-service infrastructure network, demonstrating how even seemingly basic security events can lead to major discoveries about cybercriminal operations.

To most defenders, another brute-force alert on exposed RDP is background noise — bread-and-butter activity you triage and move past. For the Huntress Tactical Response Team, however, one of those "routine" alerts turned into something very different. As they investigated a single successful login, they uncovered unusual credential-hunting behavior, a web of geo-distributed infrastructure, and a shady VPN service that all pointed toward a ransomware-as-a-service ecosystem and its initial access brokers.
The Incident Unfolds
In this case, a network was exposing an RDP server to the broader internet. While security professionals consistently warn about the dangers of this practice, many businesses have no choice but to expose RDP for operational reasons. When the Huntress Security Operations Center (SOC) received an alert for domain enumeration, they began investigating.
"Although intrusions are often written about in a linear fashion, neatly mapped to frameworks like ATT&CK, the reality is that analysts often receive signals for intrusions that are normally found in the 'middle' of a threat actor's kill chain," explained a Huntress researcher. "This means that once a signal is received, we have to work both backwards and forwards in time to find both the source of the intrusion as well as any go-forward attack paths."
Upon investigation of the Windows event logs, the team discovered that the RDP service was being brute forced. While this is a common attack technique, the investigation revealed something unusual: despite targeting multiple accounts, only one was successfully compromised. More interestingly, this single account was accessed from multiple IP addresses, suggesting a coordinated attack using distributed infrastructure rather than multiple threat actors.
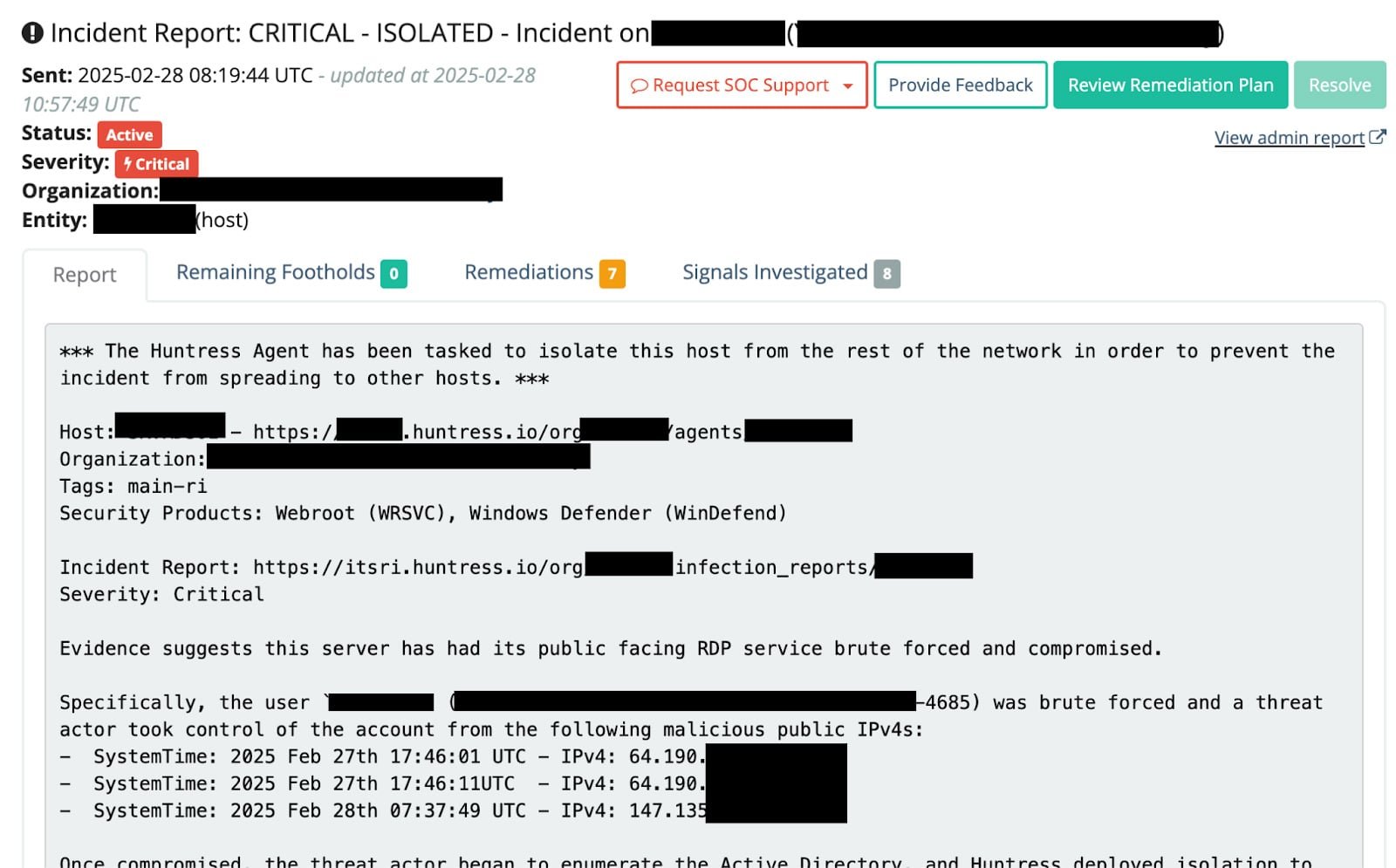 Figure 1: Initial SOC incident report showing brute forcing from multiple IP addresses
Figure 1: Initial SOC incident report showing brute forcing from multiple IP addresses
Uncovering Unusual Tradecraft
Once the threat actor gained access to the victim network, they proceeded with domain enumeration, including exploring various groups and domain configurations. When these enumeration signals were identified as malicious, the SOC issued network-wide isolation to prevent further lateral movement.
"When threat actors land inside a network, either through an RDP intrusion or through other means such as VPN compromise, they will typically enumerate the network, gather credentials and move laterally," the Huntress researcher noted. "Typically, credential access in these scenarios consists of extracting credentials from the Windows LSASS process through tooling like Procdump or Mimikatz or credential access via registry dumping."
What made this intrusion unusual was the method of credential collection. Rather than using automated tools to extract credentials from system processes, the threat actor manually searched through file systems and file shares for credentials stored in text files.
 Figure 2: Image showing domain enumeration commands
Figure 2: Image showing domain enumeration commands
"We observed the threat actor using notepad to open up text files that ostensibly contained credential materials," the researcher explained. "This uncharacteristic tradecraft prompted a second and closer examination of the IP addresses associated with the brute force attack."
The team hypothesized that most threat actors follow established playbooks for extracting credentials from system processes, while manually searching through files is more time-consuming but might reveal less obvious credentials that automated tools could miss.
Unraveling the Infrastructure
A deeper investigation of the IP addresses associated with the brute force attack revealed connections to known ransomware operations. Initial checks via malware tracking services indicated that the IPs were associated with Hive ransomware, while other reporting from the Cybersecurity and Infrastructure Security Agency (CISA) linked these addresses to BlackSuite.
When examining the TLS certificates associated with the brute-forcing IP address, the researchers discovered an interesting domain name: specialsseason[.]com. This domain name became a key pivot point for further investigation.
"The term 'Special season' also referred to as 'big game hunting' has been a common phrase used to describe financially motivated threat groups, typically ransomware targeting high-value organizations," the researcher explained.
By examining the TLS certificates fingerprint, the team found multiple related IP addresses and domain names following a consistent naming pattern: NL-.specialsseason[.]com. This revealed a geographically distributed infrastructure spanning numerous countries, including multiple locations in Russia and the United States.
Further investigation of the TLS certificates led to the discovery of another suspicious domain: 1vpns[.]com, which bears a striking resemblance to the legitimate VPN service 1vpn[.]org but with an extra 's' in the name.
"This domain name is very similar to the legitimate VPN site, but without the extra 's' after '1vpn'," the researcher noted. "We believe this is not a random naming choice but rather an attempt to mimic a legitimate service while providing criminal infrastructure."
The VPN Service Connection
The investigation revealed that the 1vpns[.]com domain advertised additional services, including 1jabber[.]com with a list of "funny" domains. Notably, one of these domains was nologs[.]club, and the VPN service FAQ emphasized their "0 logs" policy.
"A VPN service that keeps no logs would be particularly attractive to cybercriminals who want to avoid leaving traces of their activities," the researcher pointed out. "This connection between the VPN service and the ransomware infrastructure provides insight into how these actors build their support ecosystem."
Broader Implications for Defenders
This case demonstrates the importance of looking beyond the initial incident response and considering the broader context of security events. What appeared to be a straightforward brute force attack actually provided a window into the operations of initial access brokers who facilitate ransomware attacks.
"We often read about ransomware cases through a lens of techniques, tactics, procedures and other abstract elements," the researcher said. "We often hear terms like 'initial access brokers' but often do not get an inside view into their operations, particularly through an infrastructure lens. In this case, we can see how these nefarious actors operate and can get a glimpse into their motivations as well as the kinds of elements that make up their ecosystem."
For security teams, this case highlights several important takeaways:
- Don't dismiss routine alerts: Even common attack types like brute force can lead to significant discoveries when investigated thoroughly.
- Document everything: In this case, having access to detailed telemetry was crucial for understanding the full scope of the attack.
- Look for anomalies: The manual credential search method was unusual and prompted further investigation that revealed the broader infrastructure.
- Understand the criminal ecosystem: Recognizing how different components (like VPN services) support ransomware operations can help defenders anticipate attack patterns.
- Share threat intelligence: The discovery of this infrastructure provides valuable information that can help other organizations defend against similar attacks.
The researchers have published the full list of indicators of compromise (IOCs) associated with this operation, including IP addresses, domains, and certificate fingerprints, to help the broader security community detect and defend against this infrastructure.
"Ransomware continues to disrupt businesses large and small alike," the researcher concluded. "At Huntress, we are always looking to 'SOC and Awe' and are constantly pulling on every and any investigative thread that we can get our fingers on. In this case, what started out as a simple brute force attack turned out to unravel a rather large suspected ransomware-as-a-service ecosystem, specifically one that is suspected to be utilized by initial access brokers who facilitate this illicit dynamic."
For organizations looking to improve their defensive posture, Huntress offers Tradecraft Tuesday sessions, which provide cybersecurity professionals with in-depth analysis of the latest threat actors, attack vectors, and mitigation strategies. These weekly sessions feature technical walkthroughs of recent incidents, comprehensive breakdowns of malware trends, and up-to-date indicators of compromise.
As ransomware operations continue to evolve, understanding the infrastructure and support systems that enable these attacks becomes increasingly important for defenders. This case serves as a reminder that even the most common security events can provide valuable insights into the complex world of cybercrime when investigated with curiosity and thoroughness.

Comments
Please log in or register to join the discussion