
Security
Brokewell Malware Hijacks Android Devices Through Fake TradingView Ads
9/1/2025

Security
TSG Fortifies Telecom Infrastructure: New Standards Target SS7 and Diameter Vulnerabilities
9/1/2025
Security
Critical Apache Commons Text Vulnerability Exposes Widespread Remote Code Execution Risk
9/1/2025
Security
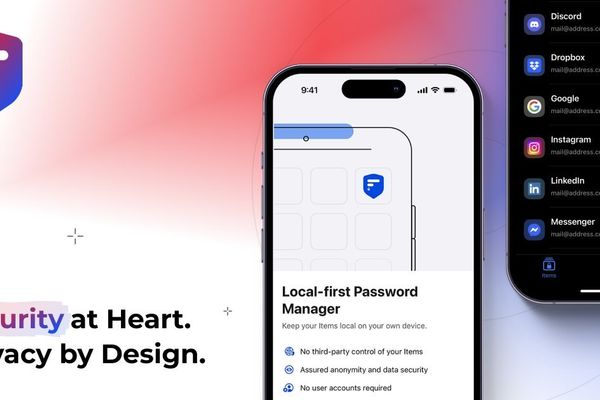
2FAS: The Open-Source Champion Simplifying Two-Factor Authentication for Everyone
8/31/2025
Security
The XZ Utils Backdoor: How a Single Malicious Commit Nearly Compromised Global SSH Security
8/31/2025

Security
Nx Build Platform Compromised: Malicious Packages Trigger Massive Secrets Leak
8/31/2025
Security
Captan CLI: Open Source Cap Table Management Revolutionizes Startup Equity Tracking
8/30/2025

Security
The Silent Swipe: Portable POS Thefts Exploit Contactless Tech in Crowded Spaces
8/10/2025
Security
The Viral Code: How 'The Game' Infected Silicon Valley with Manipulation Culture
8/10/2025

Security
RubyGems Under Siege: 275,000 Downloads of Malicious Gems Fuel Credential Theft Campaign
8/9/2025

Security
Google Confirms Salesforce CRM Breach Exposed Ads Prospects' Data in Sp1d3rHunters Attack
8/9/2025
Security
Log4Shell Revisited: How a Single Vulnerability Reshaped Software Supply Chain Security
8/9/2025

Security
AI-Powered Intrusions and Systemic Flaws: Black Hat and Defcon Unveil Critical Security Threats
8/9/2025