DevOps
SSH-Powered CI Log Viewing: Tangled's Innovative Approach to Remote Development
5/29/2026

Vulnerabilities
Linux 7.0.8 and LTS Kernels Updated to Close ssh‑keysign‑pwn
5/15/2026
Vulnerabilities
Critical Linux Kernel Vulnerability Exposes SSH Keys and Shadow Files via Race Condition
5/15/2026

Security
The Evolution of Security: From Physical Tokens to Built-in Secure Elements
5/10/2026
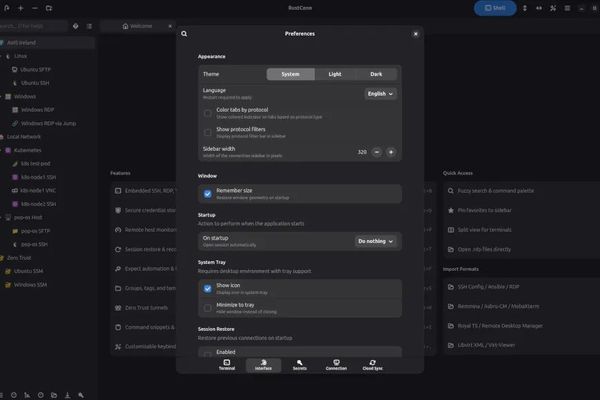
Rust
RustConn: The Modern GTK4 Connection Manager Expands With Cloud Sync, SSH Tunnel Management, and Enhanced Jump Host Support
5/4/2026
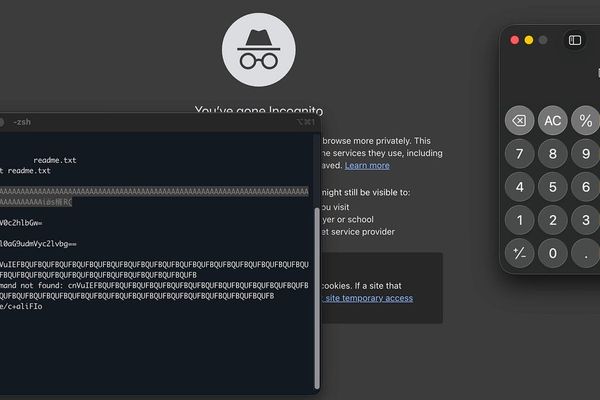
Vulnerabilities
The Hidden Danger in Terminal Emulators: How 'cat readme.txt' Became a Code Execution Vector
4/19/2026
Security
SSH Certificates: The Better SSH Experience
4/3/2026
Security
SSH Key Management: From Chaos to Security
3/13/2026
Security
Secure Snake Home: When SSH Becomes a Game
2/28/2026

Security
New Linux Botnet SSHStalker Leverages Vintage IRC Protocol for Command Control
2/11/2026
Security
The Day Telnet Went Silent: GreyNoise Labs Tracks a Vanishing Protocol
2/10/2026
DevOps
CI In a Box: Rethinking Continuous Integration with SSH Wrappers
2/6/2026
Business
JuiceSSH Licensing Controversy: When Pro Features Disappear and Users Fight Back
1/27/2026