
Security
One Missed Threat Per Week: What 25M Security Alerts Reveal About Low-Severity Risk
5/9/2026

Security
TCLBANKER Banking Trojan Targets Financial Platforms via WhatsApp and Outlook Worms
5/8/2026

Security
Microsoft Entra closes passkey security gaps with verified recovery, credential removal for enterprise identities
5/7/2026

Cybersecurity
Webinar: Why modern attacks require both security and recovery
5/7/2026
Cybersecurity
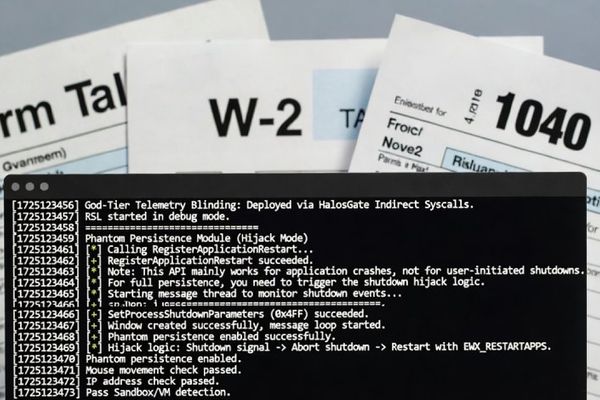
Silver Fox Deploys ABCDoor Malware via Tax-Themed Phishing in India and Russia
5/5/2026

Vulnerabilities
Critical Week in Cybersecurity: cPanel Under Attack, Linux Kernel Exploited, and GitHub RCE Emerges
5/5/2026

Security
China-Linked Hackers Launch Coordinated Espionage Campaigns Against Governments and Journalists
5/2/2026
Security
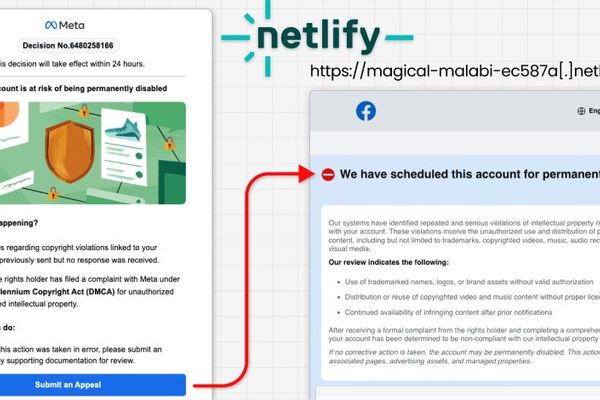
30,000 Facebook Accounts Compromised via Google AppSheet Phishing Campaign
5/2/2026
Security
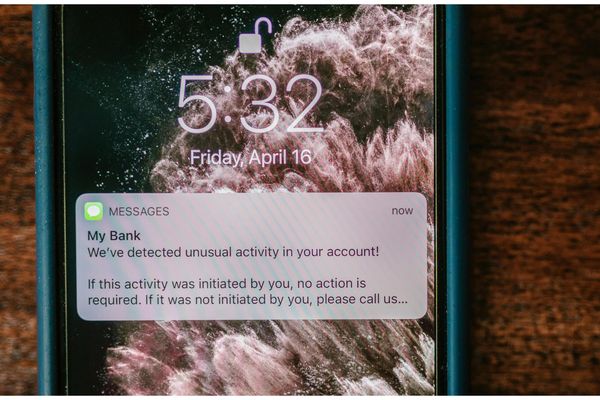
Threat Landscape Intensifies: SMS Blasters, Healthcare System Flaws, and Mass Account Hacks Highlight Growing Cybersecurity Challenges
5/1/2026
Cybersecurity
Most phishing now uses AI, says KnowBe4 • The Register
5/1/2026

Security
Canada Makes First SMS Blaster Arrests in Toronto, Exposing Growing Mobile Security Threat
4/28/2026

Vulnerabilities
Robinhood Account Creation Flaw Abused in Sophisticated Phishing Campaign
4/28/2026
Vulnerabilities
Canadian SMS Blaster Operation Disrupts 13 Million Network Connections, Blocks Emergency Services
4/27/2026